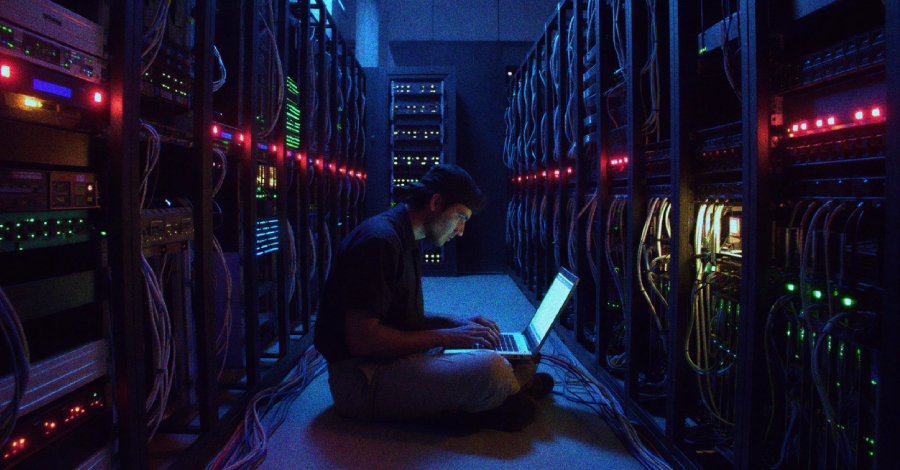
Security researchers have uncovered a campaign by an Iranian state-sponsored hacking group that has infiltrated the networks of several U.S. organizations. The group, known as MuddyWater, deployed a previously unseen backdoor called Dindoor to target entities including banks, airports, non-profits, and the Israeli subsidiary of a software company.
The findings were published by researchers from Broadcom’s Symantec division and the Carbon Black Threat Hunter Team. Their report provides technical evidence linking the recent intrusions to the long-running MuddyWater operation, which cybersecurity experts widely attribute to Iran’s Ministry of Intelligence and Security.
Technical Details of the Dindoor Backdoor
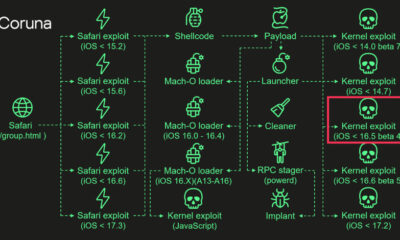
The newly identified malware, Dindoor, is a sophisticated backdoor designed to provide persistent remote access to compromised systems. Analysis shows it is capable of executing commands, uploading and downloading files, and performing reconnaissance on infected networks. Its deployment indicates an ongoing effort to maintain a foothold within critical U.S. infrastructure sectors.
MuddyWater, also tracked under names like Seedworm and TEMP.Zagros, is known for its persistent cyber espionage activities. The group typically uses spear-phishing emails with malicious documents to gain initial access, followed by the deployment of custom tools like Dindoor to move laterally through a network.
Scope and Impact of the Campaign
The campaign’s targeting of diverse sectors suggests a broad intelligence-gathering objective. While the exact number of compromised organizations was not disclosed, the inclusion of financial, transportation, and technology-related entities highlights the strategic nature of the attacks. The targeting of an Israeli software company’s office aligns with the group’s historical focus on entities related to Iran’s geopolitical interests.
There is no public evidence that the intrusions disrupted operations or destroyed data, which is consistent with MuddyWater’s profile as an espionage-focused actor. The primary goal appears to be the stealthy theft of sensitive information.
Attribution and Geopolitical Context
Attributing the activity to an Iranian state-sponsored group is based on technical indicators, infrastructure overlaps, and tactics previously documented by multiple cybersecurity firms and government agencies. MuddyWater’s operations are part of a wider landscape of state-level cyber activity emanating from Iran, often conducted in parallel with other groups like APT35.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has previously issued alerts about MuddyWater’s techniques. Such campaigns occur amidst ongoing geopolitical tensions, though the researchers’ report sticks to the technical facts of the intrusion set without speculating on political motives.
Response and Mitigation
The security firms have notified the affected organizations and shared detailed indicators of compromise (IOCs) with the broader cybersecurity community. These IOCs include file hashes, domain names, and IP addresses associated with the attacks, enabling other network defenders to search for signs of infection.
Standard security recommendations apply, including vigilance against phishing attempts, prompt patching of software, the use of multi-factor authentication, and network segmentation to limit lateral movement. Organizations in critical sectors are advised to review the published technical data.
Looking ahead, cybersecurity analysts expect MuddyWater to continue refining its tools and techniques. The disclosure of the Dindoor backdoor will likely prompt the group to modify its malware or infrastructure to evade detection. Continued monitoring and information sharing between private security firms and government agencies are anticipated as key components of the defense against such persistent threats.
Source: Broadcom Symantec, Carbon Black Threat Hunter Team