Cybersecurity researchers have identified a coordinated campaign involving five malicious software packages, or “crates,” in the Rust programming language ecosystem. These crates were designed to steal sensitive Developer Secrets by exploiting automated build and deployment pipelines. The discovery was made public in early March, highlighting an ongoing threat to software supply chain security that could impact developers and organizations globally.
Details of the Malicious Packages
The malicious crates were published on the official Rust package registry, crates.io, between late February and early March of this year. According to security firm Socket, which first uncovered the activity, the packages impersonated legitimate time-related utilities. Their primary function was to locate and exfiltrate data from .env files, which commonly store configuration secrets like API keys and database passwords, sending this information to servers controlled by the threat actors.
The five packages listed by researchers are chrono_anchor, dnp3times, time_calibrator, time_calibrators, and time-sync. These crates posed as clients for the legitimate timeapi.io service, a tactic known as “typosquatting” or “brandjacking” designed to trick developers into accidentally using the malicious code.
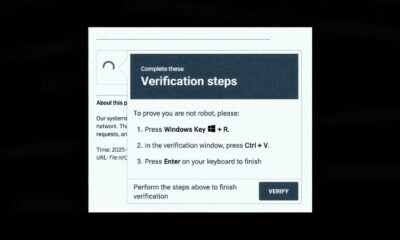
Exploitation of CI/CD Pipelines
The attack methodology specifically targeted Continuous Integration and Continuous Deployment (CI/CD) systems. These automated pipelines are used by development teams to build, test, and deploy code efficiently. When a malicious dependency is included in a project, the CI/CD system automatically downloads and executes it, often with high-level permissions to access the project’s full codebase and environment variables.
This automation provides a powerful vector for attackers. By compromising a single dependency, they can potentially gain access to a wide array of secrets across multiple projects and stages of development, from testing environments to production servers.
Industry Response and Mitigation
Following the disclosure, the malicious packages were removed from crates.io. The Rust ecosystem’s maintainers and security teams typically respond to such reports by unpublishing the offending crates to prevent further downloads. However, any projects that already integrated these dependencies may remain compromised until they update their manifests and rotate all exposed credentials.
Security experts consistently advise developers to scrutinize dependencies, use lockfiles to pin package versions, and employ security scanning tools that can detect suspicious package behaviors, such as network calls or filesystem access attempts. The incident underscores the critical importance of supply chain security in modern software development.
Broader Implications for Open Source Security
This incident is part of a persistent trend targeting open-source package repositories, including npm for JavaScript, PyPI for Python, and RubyGems for Ruby. Attackers frequently use social engineering tactics, like impersonating popular packages, to infiltrate development workflows. The goal is often financial gain through cryptomining, data theft for espionage, or laying groundwork for larger-scale attacks.
While repository maintainers work to improve automated detection and manual review processes, the ultimately decentralized and open nature of these ecosystems means vigilance is a shared responsibility between maintainers and the millions of developers who use these resources daily.
Looking ahead, security analysts expect similar campaigns to continue as attackers refine their methods. The Rust Security team and broader open-source community are likely to enhance monitoring and alert systems for crates.io. Developers and organizations are advised to audit their dependencies, implement secret management solutions, and monitor their CI/CD environments for unauthorized activity. Official post-mortem reports from the involved security researchers may provide further technical details and indicators of compromise in the coming weeks.
Source: Socket Security Research