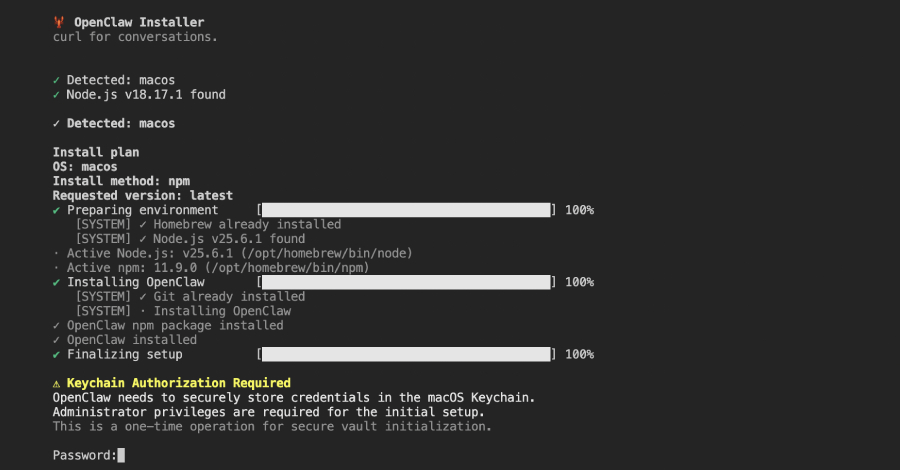
cybersecurity researchers have identified a malicious package on the npm software registry that impersonates an installer for an artificial intelligence tool to deploy a remote access trojan. The package, which targets macOS systems, is designed to steal sensitive credentials and data from compromised computers.
The malicious library, named “@openclaw-ai/openclawai,” was uploaded to the public npm registry on March 3, 2026. It was published by a user account with the name “openclaw-ai.” According to available download statistics, the package has been installed 178 times. The library remained available on the registry at the time of the discovery.
Attack Method and Payload
The package masquerades as an installer for a tool called “OpenClaw,” likely capitalizing on interest in AI-related software. When executed, the package deploys a remote access trojan, or RAT. This type of malware provides attackers with extensive control over an infected system.
On compromised macOS hosts, the RAT executes commands to harvest a wide range of sensitive information. This includes browser-stored credentials, cryptocurrency wallet data, and system files. The malware is engineered to exfiltrate this stolen data to servers controlled by the threat actors.
Context of Software Supply Chain Threats
This incident is the latest in a series of software supply chain attacks targeting open-source repositories like npm. Developers routinely use such public registries to download code libraries that serve as building blocks for applications. A single malicious package can therefore impact hundreds of downstream projects and users who trust the integrity of the registry.
Attackers frequently use “typosquatting” or brand impersonation, as seen in this case, to trick developers into downloading a malicious package instead of a legitimate one. The use of a name associated with artificial intelligence software suggests an attempt to exploit current high-demand trends.
Response and Mitigation
Security teams analyzing the package have reported their findings to npm’s maintainers for takedown. Standard advice for developers includes verifying the authenticity of package publishers, scrutinizing package metadata for signs of fraud, and using security tools that scan dependencies for known vulnerabilities and malicious code.
Organizations are encouraged to enforce strict policies regarding software provenance and to maintain an inventory of all open-source components used in their development environments. Vigilance is required even for packages that appear to come from reputable-sounding accounts or that reference popular technologies.
Ongoing Investigation and Next Steps
The investigation into the “@openclaw-ai/openclawai” package is ongoing. Researchers are working to identify the full scope of the infection, including the command and control infrastructure used by the attackers. Further analysis will aim to uncover any connections to known threat actor groups or campaigns.
Users and developers who may have installed this package are advised to scan their systems with updated antivirus software and to rotate any credentials stored on affected machines. The npm registry administrators are expected to remove the malicious package and potentially suspend the associated publisher account. Security vendors will likely add signatures for the detected RAT to their products in the coming days.
Source: GeekWire