Two Google Chrome browser extensions have been compromised following an apparent transfer of ownership, security researchers report. The extensions, which were originally legitimate tools, now function as malware delivery vehicles capable of injecting arbitrary code and stealing sensitive user data.
The affected add ons are named “QuickLens Search Screen with” and “BuildMelon.” Both were initially published by a developer using the email address “[email protected].” The extensions have since been updated with malicious code after control changed hands.
How the Malicious Extensions Operate
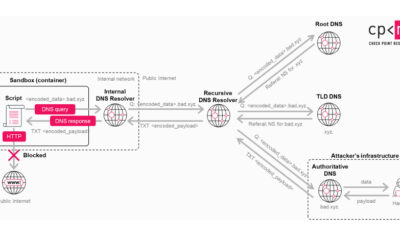
The compromised extensions abuse their permissions to execute harmful scripts on users’ devices. Once installed, they can push additional malware payloads to a victim’s computer. This allows attackers to run any code they choose, effectively taking control of the browser.
The extensions also harvest sensitive information. They are designed to collect data entered into or displayed by the browser, including login credentials, financial information, and personal details. This data is then transmitted to servers controlled by the threat actors.
The Risk of Extension Ownership Transfers
This incident highlights a significant security vulnerability within browser extension ecosystems. Developers can sell or transfer ownership of their extensions to other parties through official marketplaces like the Chrome Web Store. While this process is permitted, it introduces risk.
New owners can submit updates that fundamentally change an extension’s behavior. Since these updates are reviewed automatically in most cases, malicious code can sometimes slip through. Users who trusted the original developer may remain unaware that their trusted tool has become a threat.
Official Response and User Guidance
Google has been notified of the malicious activity. The company typically removes such extensions from the Chrome Web Store once they are identified. Users who had installed the extensions should check their browsers and remove them immediately.
Security experts recommend reviewing installed browser extensions regularly. Users should verify the publisher name and check recent update logs for any suspicious changes. It is also advised to limit extensions to only those that are absolutely necessary and come from reputable, long standing developers.
The broader security community is examining the incident to understand the full scope of the compromise. Researchers are analyzing the malicious code to determine its capabilities and potential connections to known threat groups.
Looking Ahead for browser security
This event is expected to renew discussions about security policies for browser extension marketplaces. Potential measures include more rigorous manual review for extensions following an ownership transfer, clearer user notifications when an extension’s developer changes, and enhanced monitoring for sudden behavioral shifts in established add ons.
Google and other browser vendors are likely to assess their review processes in response. Users worldwide should anticipate updated security advisories and potentially new browser features designed to flag or restrict extensions with recently changed ownership.
Source: Various Security Research Reports