Security researchers have identified a series of malicious campaigns distributing a new information stealer for Apple’s macOS operating system. The campaigns, known as ClickFix, trick users into installing what appear to be popular artificial intelligence tools, only to deploy malware designed to harvest sensitive data from their computers.
The activity involves at least three distinct ClickFix campaigns acting as a delivery mechanism for a macOS infostealer called MacSync. This method of attack does not rely on software vulnerabilities but instead depends entirely on user interaction. Targets are persuaded to copy and execute specific commands in their system’s terminal, a process that installs the malicious payload.
How the ClickFix Campaigns Operate
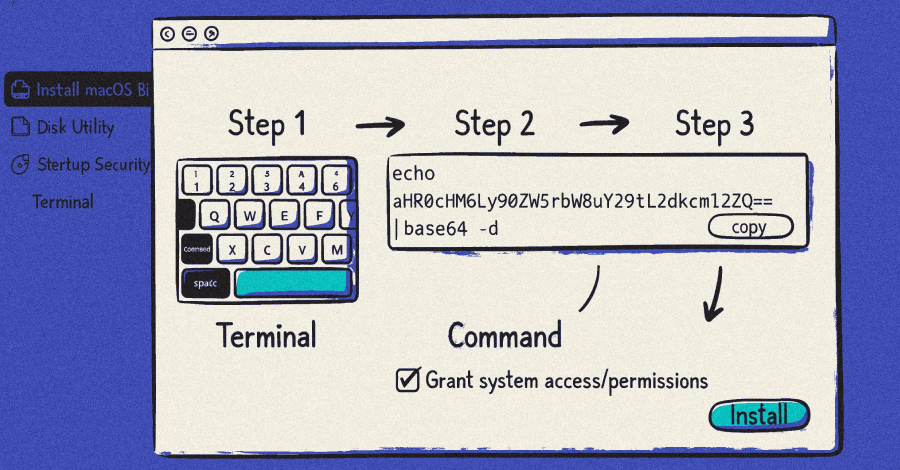
The campaigns typically begin with deceptive advertisements or posts on social media platforms and forums. These promotions offer cracked or free versions of in-demand AI software and utilities. Interested users are directed to websites hosting detailed, step-by-step instructions for the supposed installation.
These instructions require users to open the Terminal application and paste a series of commands. The commands are designed to download and execute a script from a remote server under the attackers’ control. This script then installs the MacSync infostealer onto the victim’s system without their knowledge.
Capabilities of the MacSync Malware
Once installed, MacSync is engineered to collect a wide array of sensitive information from the compromised Mac. Security analysts report that the malware can steal data from web browsers, including saved passwords, cookies, and autofill information. It also targets cryptocurrency wallets and can gather system information, which could be used for further attacks.
The stolen data is exfiltrated to a command-and-control server operated by the threat actors. This information can be used for financial fraud, identity theft, or sold to other criminals on underground cybercrime forums.
A Shift in macOS Threat Landscape
This incident highlights a continuing trend of cybercriminals increasingly targeting macOS users. While historically less frequent than Windows-based attacks, threats against Apple’s platform have grown in both sophistication and volume. The reliance on social engineering, rather than technical exploits, makes these campaigns particularly effective.
Security experts note that the attack method bypasses many traditional security checks. Because the user manually executes the commands, the malware installation is not flagged by some security tools that monitor for unauthorized software installations or exploit attempts.
Recommendations for Users
Cybersecurity professionals advise users to exercise extreme caution when encountering software offers that seem too good to be true. They strongly recommend obtaining software only from official developer websites or the Mac App Store. Users should never run terminal commands from untrusted sources, as this grants complete control of the system to the command’s author.
Maintaining updated security software designed for macOS can provide an additional layer of detection. Regularly updating the operating system and all installed applications is also crucial to patch any potential vulnerabilities that could be leveraged in future attacks.
The discovery of these campaigns has been reported to relevant platform providers, including Apple. Researchers are monitoring the associated infrastructure for signs of further activity or evolution of the threat. As AI tools remain in high demand, similar social engineering schemes are expected to continue, potentially using other enticing software as bait.
Source: Adapted from security research reports