North Korean state-sponsored hackers have been observed using phishing emails to compromise targets and then leveraging the victim’s own KakaoTalk desktop application to distribute malware to their contacts. The activity, attributed to the Konni hacking group, represents a sophisticated social engineering attack that exploits trusted communication platforms.
Attack Methodology and Attribution
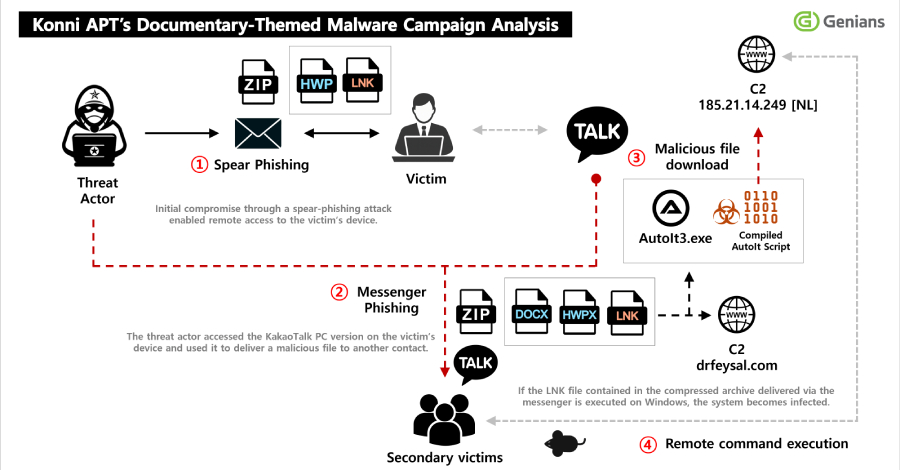
According to a report from the South Korean threat intelligence firm Genians, the campaign begins with a spear-phishing email. This email is carefully crafted to appear legitimate, tricking the recipient into opening a malicious attachment or clicking a harmful link. Once the initial compromise is successful, the attackers gain access to the victim’s computer.
The hackers then focus on the KakaoTalk desktop application, a popular messaging platform in South Korea. By using the victim’s own authenticated account, the threat actors send messages containing malicious payloads to the victim’s contacts. This method increases the likelihood of the new targets opening the files, as they appear to come from a known and trusted source.
The Konni Group’s Profile
The hacking group behind this campaign, known as Konni, has been active for nearly a decade and is widely believed by cybersecurity researchers to operate on behalf of North Korean interests. The group is known for conducting espionage campaigns targeting governments, think tanks, and organizations in South Korea and other regions. Their tactics often involve highly targeted spear-phishing and the use of remote access trojans, or RATs, to maintain control over infected systems.
In this latest campaign, the malware deployed is identified as EndRAT. This is a type of remote access tool that provides the attackers with full control over the compromised computer, allowing them to steal data, execute commands, and move laterally within a network.
Implications for Cybersecurity
This attack strategy highlights a concerning evolution in social engineering tactics. By hijacking a legitimate and widely trusted communication tool like KakaoTalk, attackers bypass many traditional security filters that might block emails from unknown external sources. The technique turns a victim’s own reputation and relationships into a weapon for further infection.
Security experts note that such attacks are particularly difficult to defend against with technical measures alone. They underscore the critical importance of user awareness training to help individuals identify sophisticated phishing attempts. Organizations are advised to implement robust endpoint detection and response, or EDR, solutions and to enforce strict application controls.
Official and Industry Response
While specific victim details are often withheld, South Korean authorities and cybersecurity agencies regularly issue alerts about campaigns attributed to North Korean actors. Companies like Genians publish detailed technical indicators of compromise, or IOCs, to help network defenders identify and block the associated malware and phishing infrastructure.
The use of messaging apps for malware propagation is not entirely new, but its adoption by a sophisticated state-sponsored group marks a significant escalation. This development has prompted security firms worldwide to update their threat models to include compromised legitimate applications as a potential attack vector.
Looking ahead, cybersecurity analysts expect the Konni group and similar threat actors to continue refining this hybrid approach. Future campaigns may target other popular regional messaging applications beyond KakaoTalk. The ongoing investigation by threat intelligence firms will likely reveal more technical details about the EndRAT malware and the full scope of the campaign, leading to updated security advisories and defensive recommendations for at-risk organizations.
Source: Genians Threat Intelligence Report