Security researchers have identified a new malware campaign that has compromised more than 14,000 network edge devices, primarily Asus routers, to create a stealthy proxy botnet. The malicious software, known as KadNap, was first observed in active attacks in August 2025 and is designed to secretly route internet traffic for cybercriminals.
According to a report from the Black Lotus Labs team at Lumen Technologies, over 60 percent of the infected devices are located within the United States. The botnet’s primary function is to act as a proxy network, allowing attackers to hide the origin of malicious web traffic, which can include credential theft, fraud, and other illicit activities.
Infection Vector and Malware Function
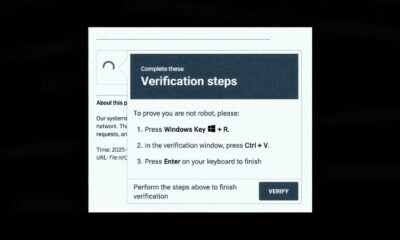
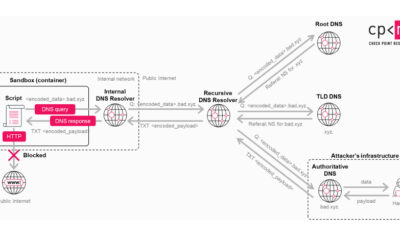
KadNap malware exploits vulnerabilities in consumer-grade routers and other internet-facing hardware to gain initial access. Once a device is infected, it connects to a command and control server operated by the attackers. The compromised device is then silently enrolled into a peer-to-peer proxy network.
This network, often referred to as a residential proxy botnet, uses the hijacked internet connections of ordinary users. This makes malicious traffic appear to originate from legitimate, geographically dispersed homes and businesses, complicating efforts by security teams to block it based on location or IP reputation.
Scale and Geographic Impact
The infection of over 14,000 devices underscores the significant scale of the operation. The high concentration of victims in the U.S. suggests the threat actors may be targeting specific network infrastructure or internet service providers prevalent in that region. Researchers continue to monitor for infections in other countries.
Edge devices like routers are attractive targets for cybercriminals because they are often poorly secured, infrequently updated, and provide constant, high-bandwidth internet access. Their compromise typically goes unnoticed by the device owner, allowing botnets to persist for long periods.
Mitigation and Security Recommendations
Black Lotus Labs has notified internet service providers about the infections to help with remediation. For individual users and network administrators, the key defense is to ensure all edge devices are running the latest firmware provided by the manufacturer.
Experts recommend changing default administrator passwords, disabling remote management features that are not strictly necessary, and regularly rebooting routers, which can sometimes disrupt temporary malware infections. Network monitoring for unusual outgoing traffic can also help identify a compromised device.
Ongoing Investigation and Future Outlook
The discovery of the KadNap botnet is part of an ongoing investigation by cybersecurity firms. Researchers are analyzing the malware’s code to understand its full capabilities and to identify links to known threat actor groups. The botnet’s infrastructure is being tracked for potential takedown operations.
Security analysts expect similar campaigns targeting internet-of-things and network edge devices to continue. The cybersecurity community anticipates further disclosures of technical indicators of compromise, which will allow for more widespread detection and blocking of the KadNap malware. Efforts to dismantle the proxy network’s command servers are likely to proceed in coordination with law enforcement and industry partners.
Source: Black Lotus Labs at Lumen Technologies