Security researchers have identified a new campaign where threat actors are impersonating IT support staff to deploy a powerful command-and-control framework called Havoc. The activity, detected last month by the security firm Huntress, targeted at least five organizations and is considered a precursor to potential data theft or ransomware deployment.
Campaign Mechanics and Initial Intrusion
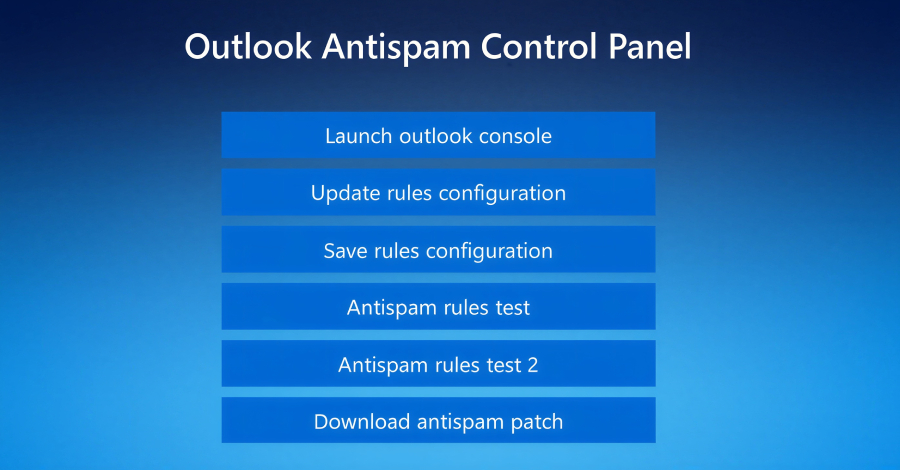
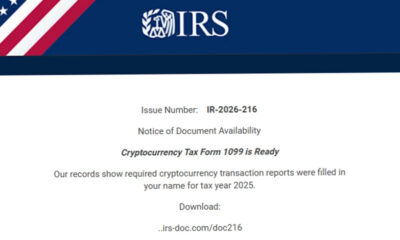
The operation begins with email spam sent to employees within an organization. These messages are designed to appear as routine IT or technical support communications. Shortly after the email is delivered, the target receives a follow-up phone call from an individual claiming to be from the support team, attempting to legitimize the initial contact and build trust.
This dual-vector approach of email and phone, often called vishing or phone phishing, increases the likelihood of a successful social engineering attack. If the target engages, they are guided to execute malicious actions, which ultimately lead to the installation of the Havoc framework on the compromised system.
The Havoc Command-and-Control Framework
Havoc is a sophisticated, open-source post-exploitation toolkit that provides attackers with extensive control over an infected machine. Security analysts describe it as a modern adversary simulation framework that is highly customizable and evades many common security detection measures.
Once installed, Havoc acts as a command hub, allowing the threat actors to remotely control the compromised computer. From this position, they can move laterally across a network, escalate privileges, steal credentials, and deploy additional payloads. Its presence is a strong indicator of an impending serious incident, such as large-scale data exfiltration or the locking of systems with ransomware.
Implications for Organizational Security
The campaign highlights the evolving tactics of cybercriminals who are blending digital and human interaction to bypass technical defenses. Traditional email filters may not catch all spam, and the personal phone call adds a layer of persuasion that pure email phishing lacks.
Security experts emphasize that this method specifically targets human psychology and organizational procedures. The fake support persona exploits the common workplace dynamic where employees are expected to comply with requests from perceived authority figures in the IT department.
Recommended Defensive Measures
In response to this threat, security professionals advise organizations to reinforce employee training on social engineering tactics. Staff should be instructed to verify unsolicited support contacts through official, independent channels before taking any action.
Technical defenses should include robust endpoint detection and response (EDR) solutions capable of identifying the behavioral patterns associated with tools like Havoc. Network monitoring for unusual lateral movement and outbound connections to unknown servers is also critical for early detection.
Furthermore, organizations are encouraged to implement strict verification protocols for any remote support requests, regardless of the initial communication method.
Ongoing Investigation and Future Outlook
Huntress continues to investigate the campaign to identify the full scope of the attacks and the specific threat actor group responsible. The security firm is sharing indicators of compromise (IOCs) and technical details with the broader cybersecurity community to aid in detection efforts.
Industry analysts expect to see further adaptation of this hybrid attack method, as it has proven effective. Organizations worldwide are advised to treat any unsolicited IT contact with heightened skepticism and to review their incident response plans for social engineering scenarios. Law enforcement agencies in multiple jurisdictions have been notified of the campaign’s activity.
Source: Huntress