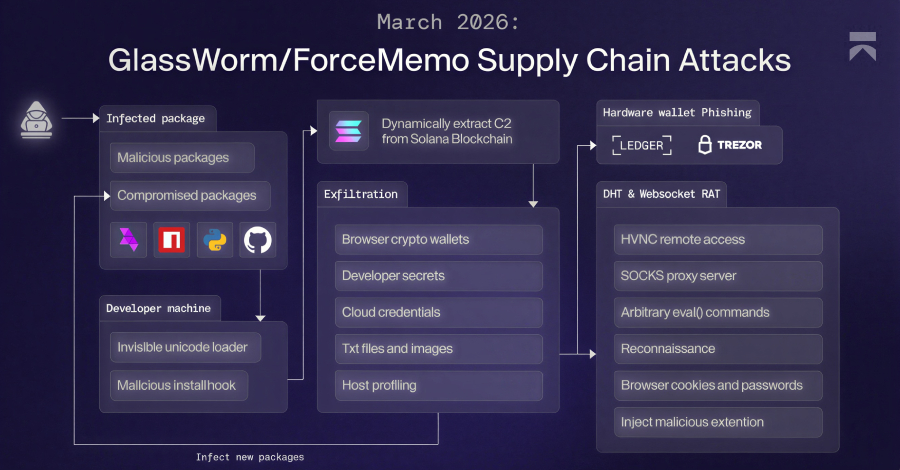
cybersecurity researchers have identified a significant evolution in the GlassWorm malware campaign, which now employs the Solana blockchain to deliver a sophisticated multi-stage attack framework. This new variant is designed to steal a wide range of sensitive data and install a remote access trojan (RAT), posing a serious threat to individuals and organizations globally. The campaign’s use of a public blockchain for covert communication marks a notable shift in malware distribution tactics.
Campaign Mechanics and data theft
The updated GlassWorm operation functions as a multi-stage infection chain. The initial payload retrieves subsequent modules capable of comprehensive information theft. One core component is a malicious Google Chrome extension that disguises itself as an offline version of Google Docs. Once installed, this extension performs extensive surveillance and data harvesting from the victim’s browser.
According to researchers, the extension logs keystrokes, dumps cookies and session tokens, and captures screenshots. This allows attackers to gain unauthorized access to online accounts, including email, social media, and financial services, by hijacking active user sessions.
Integration of Remote Access and Cryptocurrency Focus
Beyond the information-stealing extension, the GlassWorm framework deploys a full remote access trojan. This RAT provides attackers with persistent backdoor access to compromised systems, enabling them to execute commands, upload additional tools, and exfiltrate files directly.
A key feature of this campaign is its specific targeting of cryptocurrency data. The malware actively seeks out and steals information related to digital wallets, browser-stored crypto keys, and transaction histories. This focus aligns with the campaign’s novel use of the Solana blockchain for “dead drop” communications.
The Solana “Dead Drop” Technique
The term “dead drop” in espionage refers to a method of secretly leaving items or information in a predetermined location for another party to retrieve. GlassWorm adapts this concept to the digital realm by using the Solana blockchain as its covert communication channel.
Instead of using traditional, more easily monitored command-and-control servers, the malware embeds instructions and configuration data within transactions on the Solana blockchain. The infected machine reads these public transactions to receive updates and commands, making the traffic blend in with normal blockchain activity and complicating detection for network security tools.
Implications and Defense Recommendations
The combination of a multi-stage payload, a browser-based data stealer, a persistent RAT, and blockchain-based communication makes GlassWorm a particularly resilient and stealthy threat. Its ability to steal browser sessions and cryptocurrency data presents a direct financial risk to victims.
Security professionals advise heightened vigilance regarding browser extensions, recommending users only install them from official web stores and carefully review permissions. Organizations are encouraged to monitor network traffic for unexpected connections to blockchain networks as part of a broader defense-in-depth strategy.
Researchers expect further analysis of the malware’s code to reveal additional capabilities and potential links to known threat actors. Law enforcement and cybersecurity firms are likely to increase scrutiny of blockchain transactions for malicious payloads, a practice that may become more common as other threat groups adopt similar techniques. The ongoing investigation aims to identify the infrastructure behind the campaign and develop more robust detection signatures.
Source: Cybersecurity Research Reports