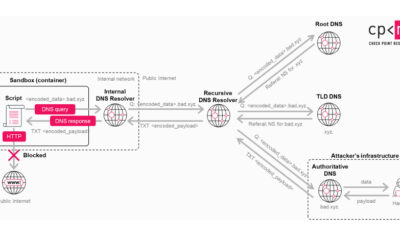
Cybersecurity researchers have identified an ongoing campaign where threat actors are exploiting FortiGate Next-Generation Firewall appliances to gain initial access to organizational networks. The attackers are leveraging recently disclosed security flaws or weak administrative credentials to steal sensitive configuration data, according to security analysts.
This activity allows malicious actors to use the network security devices themselves as a primary entry vector. Once access is achieved, the focus shifts to extracting critical configuration files from the compromised FortiGate systems.
Method of Attack and Stolen Data
The attackers target these firewalls to obtain files that contain detailed network architecture information and, critically, service account credentials. These service accounts often possess elevated privileges and are used for system-to-system communication across the IT environment.
Possession of these credentials grants attackers significant lateral movement capabilities within a breached network. With valid service account credentials, they can authenticate to various internal systems, servers, and applications, often with minimal detection, as the activity appears legitimate.
Background on the Vulnerabilities
While the specific vulnerabilities used may vary across incidents, Fortinet has disclosed several critical security flaws in its FortiGate OS in recent months. The company routinely issues patches and security advisories urging customers to update their systems promptly.
In many security breaches, however, attackers exploit known vulnerabilities for which patches already exist. This highlights a common challenge in cybersecurity: the gap between a patch’s release and its widespread deployment across all vulnerable devices in an organization.
Implications for Network Security
The campaign underscores a strategic shift by threat actors towards targeting the very appliances designed to protect network perimeters. Firewalls, especially next-generation models like FortiGate, manage inbound and outbound traffic and store crucial network blueprints.
A compromise of such a device is particularly severe. It not only breaches the first line of defense but also provides attackers with a roadmap of the internal network and keys to move through it stealthily.
Security experts emphasize that stolen service account credentials are highly valuable. Unlike individual user accounts, which can be monitored and disabled, service accounts are frequently excluded from standard password rotation policies and multifactor authentication requirements, making them persistent and powerful tools for attackers.
Recommended Mitigation Steps
In response to this threat pattern, cybersecurity professionals recommend several immediate actions for organizations using FortiGate or similar firewall technologies. The primary recommendation is to ensure all devices are running the latest firmware versions, with all critical security patches applied without delay.
Additionally, organizations are advised to audit and strengthen all administrative credentials for network devices, enforcing complex, unique passwords and implementing multifactor authentication where supported. Regular reviews of active service accounts and their permissions are also considered a essential security practice.
Network segmentation is cited as a crucial defensive strategy to limit the potential damage from lateral movement, even if initial breach occurs. This involves dividing the network into smaller zones to contain the spread of an attacker who gains a foothold.
Looking ahead, security researchers and vendors like Fortinet are expected to continue monitoring this campaign closely. Further technical details on the indicators of compromise and specific malware families involved may be released as the investigation progresses. Organizations globally are urged to treat their network security appliances as high-value targets requiring vigilant maintenance and monitoring.
Source: Cybersecurity Researchers