A significant security vulnerability in a widely used third-party Android software development kit (SDK) has been patched after potentially exposing the private data of approximately 50 million users. The flaw, discovered in the EngageLab SDK, specifically impacted an estimated 30 million installations of cryptocurrency wallet applications, raising substantial concerns over digital asset security. The issue, which has now been resolved, allowed malicious applications on a compromised device to bypass standard Android security protections.
Scope and Mechanism of the Vulnerability
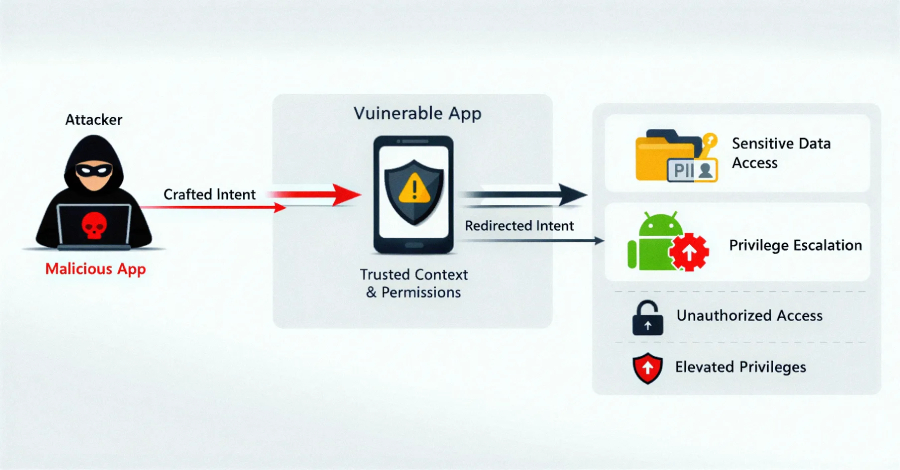
Microsoft’s Defender for Endpoint research team, which identified and reported the flaw, stated that the vulnerability permitted unauthorized cross-application data access. “This flaw allows apps on the same device to bypass Android security sandbox and gain unauthorized access to private data,” the security team explained. The EngageLab SDK is integrated into various Android applications to handle push notification services, making it a common component across a diverse range of software.
The core of the security failure involved the SDK’s improper implementation of content providers, a standard Android mechanism for data sharing. Researchers found it was configured to be globally accessible, meaning any application installed on the device could query it without requiring specific permissions. This misconfiguration effectively broke the application sandbox, a fundamental security layer in the Android operating system designed to keep app data isolated.
Implications for Cryptocurrency Users
The exposure of cryptocurrency wallet applications represents the most critical aspect of this incident. With an estimated 30 million wallet installs affected, the flaw could have allowed a malicious actor to potentially access sensitive information such as wallet addresses, transaction histories, and other private data stored by the wallet apps. Security experts note that while the vulnerability did not directly expose private keys stored in secure hardware elements, the harvested data could be used for highly targeted phishing attacks or to map a user’s financial activity.
The broad installation base of the EngageLab SDK, totaling around 50 million user devices according to the researchers, indicates that non-crypto applications were also at risk. Any app using the vulnerable SDK version could have had its private application data accessed by another malicious app on the same phone.
Discovery and Remediation Timeline
Microsoft’s security researchers discovered the vulnerability and followed coordinated disclosure practices by notifying EngageLab. The SDK developer subsequently addressed the security hole. A patched version of the EngageLab SDK has been released to developers. It is now the responsibility of individual app developers and companies to integrate the updated, secure SDK version into their applications and push the updated apps to users via official stores like Google Play.
Google was also informed of the vulnerability. The company can use its Play Protect security services to detect and warn users about applications that contain known, unpatched vulnerabilities, adding another layer of user protection.
Recommendations for Developers and Users
For developers who integrated the EngageLab SDK into their applications, the immediate required action is to update to the patched SDK version and release an updated application build as swiftly as possible. Security best practices dictate regular dependency checks to ensure all third-party code components are up-to-date and free from known vulnerabilities.
For Android users, general security guidelines apply. Users should ensure their devices are updated with the latest operating system and security patches. Installing applications only from official and trusted sources like the Google Play Store reduces risk, as does being cautious about granting unnecessary permissions to apps. Users of cryptocurrency wallets are advised to confirm with wallet providers that their application is using the latest, secure version of any integrated SDKs.
Looking Forward: Ecosystem Security Challenges
The incident underscores the persistent security challenges within the mobile application ecosystem, particularly concerning supply chain risks from third-party SDKs. These software kits provide valuable functionality for developers but can introduce widespread vulnerabilities if not properly secured. The expected next phase involves the gradual rollout of updated applications by developers who depend on the EngageLab SDK. Users worldwide are awaiting these updates to fully mitigate the risk, a process that can take weeks or months depending on developer responsiveness. Security analysts will continue to monitor for any attempted exploitation of this flaw before the patch is universally deployed.
Source: Microsoft Security Research