Security researchers have identified an ongoing phishing campaign exploiting Microsoft’s device code authentication to compromise accounts across more than 340 organizations. The attacks, first detected on February 19, 2026, have targeted entities in the United States, Canada, Australia, New Zealand, and Germany.
The campaign specifically abuses the OAuth 2.0 device authorization grant flow, a legitimate feature designed to let users sign in on devices with limited input capabilities, such as smart TVs or gaming consoles. Threat actors are using this mechanism to trick users into granting access to their Microsoft 365 environments.
How the Attack Works
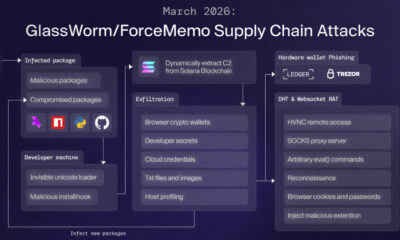
In a typical attack sequence, the threat actor initiates a device code login request for a targeted Microsoft service. This generates a user code and a verification URL, often pointing to Microsoft’s official login.live.com or microsoft.com domains. The attacker then embeds this code into a phishing email or message, urging the victim to visit the URL and enter the code to verify their identity or resolve a purported security issue.
When the victim enters the code on the legitimate Microsoft page, they are prompted to approve permissions for a malicious OAuth application registered by the attacker. If the user grants consent, the application receives an access token, allowing the attacker to impersonate the user and access their Microsoft 365 data, including email, files, and contacts, without needing the victim’s password.
Scope and Detection
The cybersecurity firm Huntress first reported on this activity. They noted a significant acceleration in the number of cases following the initial detection. The campaign’s cross-border nature, affecting organizations in five countries, underscores its broad targeting.
This method is particularly effective because it bypasses multi-factor authentication (MFA) protections. The authentication occurs on a legitimate Microsoft site, making traditional phishing indicators less obvious. The malicious access is gained through consented application permissions, which can be difficult for standard security tools to flag as anomalous.
Mitigation and Response
Microsoft and security advisors recommend several immediate actions for organizations. Administrators should audit and review all consented OAuth applications within their Azure Active Directory or Microsoft 365 admin centers, removing any that are unfamiliar or unnecessary. Implementing conditional access policies to restrict user consent for OAuth applications is also a critical step.
Furthermore, security teams are advised to monitor sign-in logs for authentication flows using the “device code” grant type, especially those originating from unexpected locations or associated with newly registered applications. User awareness training is crucial, as employees must be educated to scrutinize permissions requested by any application, even when prompted on a genuine Microsoft login page.
Based on the current trajectory, security analysts expect similar campaigns to continue targeting cloud identity systems. Organizations worldwide are likely to receive updated guidance from Microsoft and national cybersecurity agencies in the coming weeks. The focus will remain on hardening OAuth application governance and improving detection of anomalous consent grants.
Source: Huntress