A newly identified malware loader, dubbed DeepLoad, is being distributed through a sophisticated social engineering campaign targeting users worldwide. The campaign employs a tactic known as “ClickFix” to trick victims into installing the malicious software, which then uses advanced techniques to steal sensitive browser credentials and maintain persistence on infected systems.
Campaign Mechanics and Initial Infection
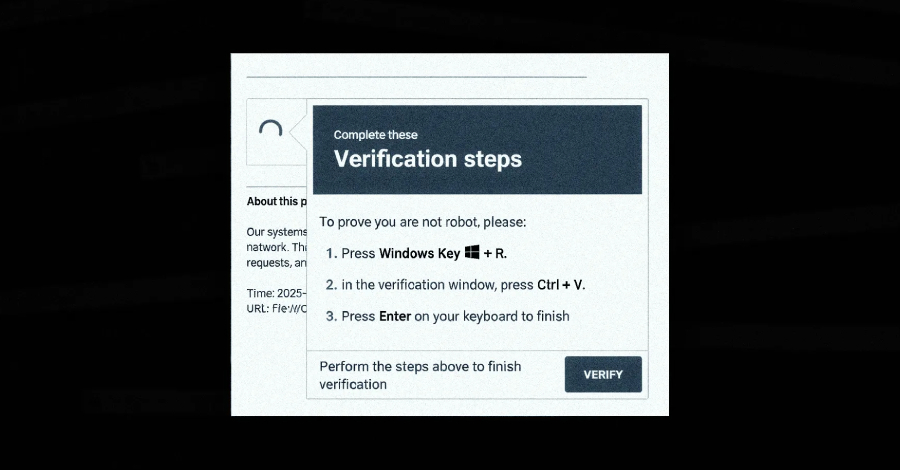
Security researchers from ReliaQuest have documented the campaign. The attack begins with the ClickFix social engineering method. This tactic typically involves presenting users with a fake error message or prompt that urges them to click a button or link to “fix” a non-existent problem with their system or software.
Once a user interacts with this prompt, the DeepLoad malware loader is deployed onto the victim’s computer. Researchers note that DeepLoad was previously undocumented, indicating it is a new tool in the cybercriminal arsenal.
Evasion and Credential Theft Capabilities
The malware employs several methods to avoid detection and ensure it can carry out its primary function of stealing data. According to ReliaQuest researcher Thassanai, DeepLoad likely uses AI-assisted code obfuscation and process injection to evade static antivirus scanning.
More critically, the credential theft module operates with high urgency. The researchers state that theft begins immediately and is designed to capture passwords and active browser sessions. This process is engineered to continue even if the primary DeepLoad loader component is subsequently blocked or removed from the system.
Persistence Through WMI
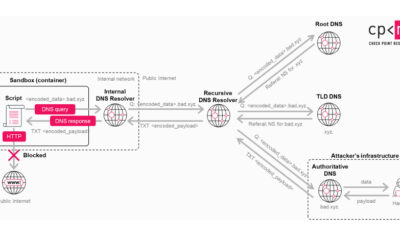
To maintain long-term access on compromised machines, DeepLoad leverages Windows Management Instrumentation (WMI). WMI is a legitimate Windows administration framework that allows for scripting and automation of system management tasks.
By abusing WMI, the malware can create persistent mechanisms that reactivate the malicious code after a system reboot or when specific conditions are met. This use of a trusted system tool makes the malware harder to detect and remove using conventional methods.
Implications for Security
The emergence of DeepLoad highlights several concerning trends in the cybersecurity landscape. The combination of effective social engineering, new malware loaders, and the abuse of legitimate system tools like WMI presents a significant challenge for both individual users and corporate security teams.
The immediate commencement of credential theft suggests the operators prioritize data capture over other activities, aiming to harvest valuable login information before the infection is discovered. The theft of browser sessions is particularly dangerous, as it can allow attackers to bypass multi-factor authentication and gain direct access to online accounts.
Recommendations and Next Steps
Security professionals advise users to be extremely cautious of unsolicited pop-ups or error messages, especially those urging immediate action. Verifying software updates directly through official vendor websites, rather than through prompts, is a key defensive practice.
Organizations are expected to monitor for suspicious WMI event subscriptions and process injection patterns as part of their threat-hunting activities. Researchers anticipate that further analysis of DeepLoad will reveal more about its infrastructure and potential connections to other known threat actors. Security firms are likely to release more detailed indicators of compromise (IOCs) and detection rules in the coming days to help the wider community defend against this threat.
Source: ReliaQuest