A recent cybersecurity bulletin highlights a shift towards sophisticated, low-profile threats, including progress in post-quantum cryptography, the weaponization of artificial intelligence for vulnerability discovery, and the widespread availability of advanced phishing kits. The report, compiled from global threat intelligence, indicates a move away from high-impact attacks towards more insidious and persistent methods that exploit systemic complacency.
Post-Quantum Cryptography Initiatives
Governments and standards bodies are accelerating efforts to transition to post-quantum cryptographic algorithms. This push is driven by the potential future threat quantum computers pose to current encryption standards. The National Institute of Standards and Technology in the United States is finalizing its PQC standards, a process that will guide global technology infrastructure updates to protect data against future decryption by quantum machines.
AI in Offensive Security
Security researchers report a significant increase in the use of artificial intelligence and machine learning tools to automate the discovery of software vulnerabilities. These AI-powered systems can scan code and networks at unprecedented scale and speed, identifying potential weaknesses for exploitation. This development lowers the barrier to entry for threat actors, enabling more sophisticated attacks from a wider pool of malicious actors.
Pirated Software as a Threat Vector
Cybercriminals are increasingly using pirated software and cracked applications as delivery mechanisms for malware. These traps, often found on unofficial download sites, bundle legitimate-looking software with backdoors, trojans, or ransomware. Users seeking to avoid licensing fees inadvertently compromise their systems, leading to data theft or extortion.
Commercial Phishing Infrastructure
The cybercrime-as-a-service ecosystem continues to expand, with phishing kits and fraudulent infrastructure being sold openly on dark web forums. These kits provide turnkey solutions for creating convincing fake login pages for banks, social media platforms, and corporate networks. Their availability enables even low-skilled criminals to launch effective credential-harvesting campaigns.
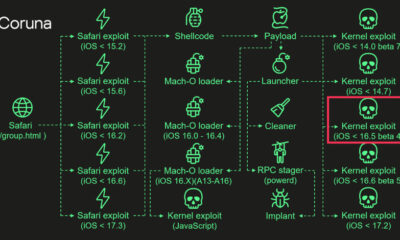
Resurgence of Established Threats
The bulletin also notes the re-emergence of older attack methods in more potent forms. This includes refined social engineering tactics and the abuse of legitimate cloud and web services to host malicious content. These methods allow attackers to blend in with normal internet traffic, making detection more challenging for security systems.
Global Implications and Response
The convergence of these trends presents a complex challenge for organizational and national cybersecurity defenses. The stealthy nature of these threats requires a shift in defensive strategies towards continuous monitoring, robust patch management, and user education. International law enforcement agencies are increasing collaboration to dismantle the infrastructure supporting phishing kits and malware distribution networks.
Looking forward, the cybersecurity community anticipates continued refinement of AI-driven attack tools and further integration of PQC standards into mainstream software. Organizations are advised to begin inventorying systems that use cryptographic protocols and to prioritize security awareness training to combat socially engineered threats. The implementation of new cryptographic standards is expected to be a multi-year process for critical infrastructure sectors worldwide.
Source: Various Global Threat Intelligence Feeds