Microsoft has disclosed a widespread social engineering campaign, dubbed ClickFix, that uses the Windows Terminal application to deploy the Lumma Stealer malware. The activity, observed in February 2026, represents a significant evolution in attack methods by exploiting a trusted system tool to initiate a sophisticated infection chain.
Campaign Mechanics and Infection Chain
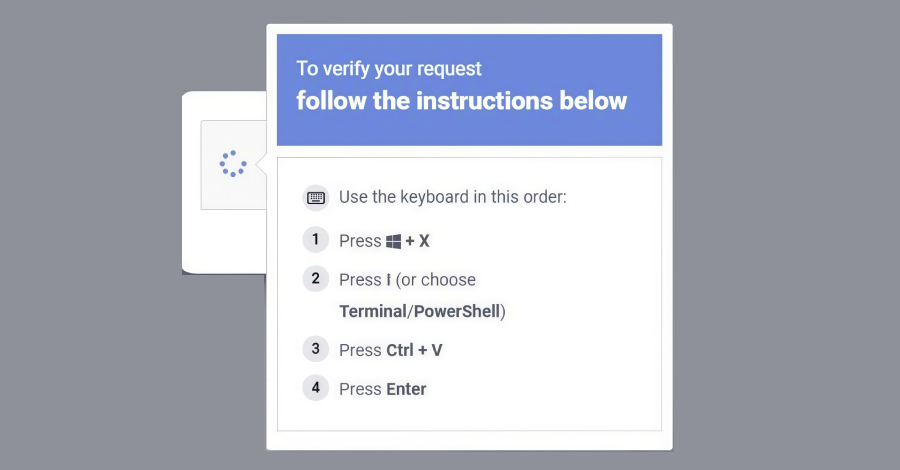
The ClickFix campaign operates by tricking users into executing malicious commands directly within the Windows Terminal, a legitimate application developers and power users rely on for system management. Traditionally, similar attacks have instructed victims to use the Windows Run dialog. By shifting to the terminal, threat actors bypass certain user suspicions associated with the Run command and leverage the terminal’s inherent permissions.
Attackers deliver the initial lure through social engineering channels, such as phishing emails or fraudulent online advertisements. The messages convince users to copy and paste a specific command into Windows Terminal. This command does not immediately download the malware, a common red flag, but instead fetches a secondary script from a remote server.
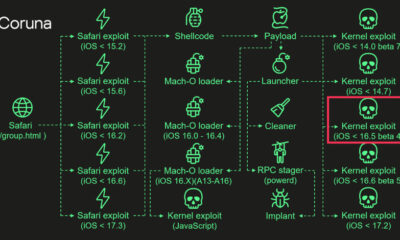
This secondary script is responsible for the core malicious activities. It downloads and executes the Lumma Stealer payload, a sophisticated information-stealing malware. The entire process is designed to be stealthy, utilizing the terminal’s normal operations to mask the malicious activity from both the user and some security software.
Capabilities of the Lumma Stealer Payload
Lumma Stealer is a potent malware family known for its data exfiltration capabilities. Once installed on a victim’s machine, it conducts a comprehensive search for sensitive information. This includes credentials stored in web browsers, cryptocurrency wallet data, and files from the desktop and document folders.
The malware is designed to harvest authentication cookies, which can allow attackers to bypass password requirements and maintain persistent access to online accounts, even those protected by two-factor authentication in some cases. All stolen data is systematically encrypted and transmitted back to servers controlled by the cybercriminals.
Significance and Security Implications
Microsoft’s disclosure highlights a concerning trend where attackers are increasingly weaponizing trusted, pre-installed system tools. The use of Windows Terminal provides a layer of camouflage, as its execution is a routine activity for many professionals. This tactic complicates detection for both users and endpoint protection systems that may whitelist activity from such trusted applications.
The campaign’s global nature targets a wide range of users, but its reliance on social engineering means that technical awareness is a primary defense. Security researchers note that the attack does not exploit a vulnerability in Windows Terminal itself, but rather manipulates user behavior to misuse the tool.
Recommended Mitigations and Next Steps
Microsoft has updated its Defender antivirus and other security products to detect the known indicators of compromise associated with the ClickFix campaign. The company advises users and IT administrators to exercise extreme caution with unsolicited instructions to run commands, regardless of the suggested application.
Enabling controlled folder access in Windows security can help block unauthorized changes to files in sensitive directories. Network defenders are recommended to monitor for outbound connections to unfamiliar command and control servers, a hallmark of Lumma Stealer activity.
Looking ahead, security analysts expect threat actors to continue refining this technique, potentially targeting other legitimate system administration tools. Microsoft and independent security firms are monitoring for new variants of the campaign. Further technical details and indicators of compromise are anticipated to be released through official security advisories to aid corporate security teams in bolstering their defenses.
Source: Microsoft Security Threat Intelligence