Cisco Systems has confirmed that two security vulnerabilities in its Catalyst SD-WAN Manager software are now being actively exploited by attackers. The company disclosed the active exploitation in a security advisory, urging customers to apply available patches immediately to secure their network management systems.
The vulnerabilities affect the web-based management interface of the Catalyst SD-WAN Manager, previously known as SD-WAN vManage. This platform is a central component for configuring, monitoring, and troubleshooting software-defined wide area networks for many enterprise organizations globally.
Details of the Exploited Vulnerabilities
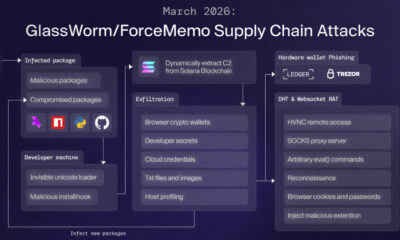
The first flaw, tracked as CVE-2026-20122, carries a CVSS severity score of 7.1. Cisco describes it as an arbitrary file overwrite vulnerability. This weakness could allow an authenticated, remote attacker to overwrite arbitrary files on the underlying file system of an affected device.
The second vulnerability, identified as CVE-2026-20123, has not yet been fully detailed in public advisories. Cisco’s confirmation indicates that both issues are part of the same attack chain being used in the wild. The company typically releases full technical details after a mitigation period to allow users time to patch.
Immediate Response and Mitigation
Cisco has released software updates that address these vulnerabilities. The company states there are no workarounds that mitigate these flaws, making patching the only complete solution. Administrators are advised to upgrade to a fixed release of the Catalyst SD-WAN Manager software.
The confirmation of active exploitation elevates the urgency for network administrators. When vulnerabilities are actively used by threat actors before most organizations can patch, the risk of widespread compromise increases significantly. Cisco’s Product Security Incident Response Team (PSIRT) is investigating the exploitation activity.
Background on SD-WAN Security
Software-defined wide area networking technology is widely adopted to connect enterprise branches, data centers, and cloud services. The management console for these networks is a high-value target for attackers because it controls the configuration and policy for an entire organization’s connectivity.
Security researchers have frequently highlighted the risks associated with network management interfaces being exposed to the internet. A compromise of a system like Catalyst SD-WAN Manager can provide attackers with a powerful foothold within an enterprise network, enabling further lateral movement and data theft.
Recommended Actions for Organizations
Organizations using Cisco Catalyst SD-WAN Manager should prioritize applying the relevant security updates provided by Cisco. They should also review access controls to the management interface, ensuring it is not unnecessarily exposed to the public internet.
Standard security practices, such as implementing network segmentation and monitoring for anomalous authentication attempts or configuration changes, are advised. Cisco provides specific version information and upgrade paths in its official security advisory.
Looking ahead, Cisco is expected to provide more detailed information about the nature of the attacks and any indicators of compromise associated with the exploitation. The company’s ongoing investigation may lead to further updates or guidance for the security community and customers. Organizations should monitor Cisco’s security advisory portal for the latest official information.
Source: Cisco Security Advisory