A suspected China-based cyber espionage operation has been targeting military organizations across Southeast Asia in a state-sponsored campaign active since at least 2020. Researchers from Palo Alto Networks Unit 42 are tracking the threat activity, which uses malware known as “AppleChris” and “MemFun” to infiltrate systems.
The campaign, tracked under the identifier CL-STA-1087, demonstrates significant operational patience and strategic targeting. The “CL” refers to cluster, while “STA” denotes a state-backed motivation, indicating the attacks are likely conducted with national resources and objectives.
Campaign Details and Malware Analysis
The primary goal of the operation appears to be cyber espionage, focusing on gathering sensitive military and strategic intelligence. The attackers have employed two distinct pieces of malware to achieve persistence and steal data from compromised networks.
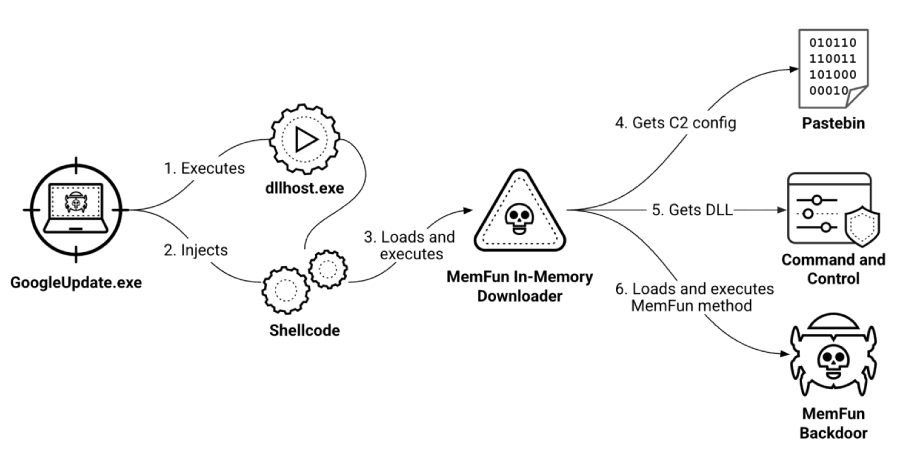
The first, dubbed “AppleChris,” is a sophisticated backdoor capable of executing commands, uploading and downloading files, and performing system reconnaissance. The second tool, “MemFun,” is a memory-based execution utility that allows the attackers to run malicious code directly in a system’s RAM, leaving fewer traces on the hard drive and evading traditional file-based detection.
Targets and Geographic Focus
The threat actors have concentrated their efforts on military entities within Southeast Asia. While specific countries have not been publicly named by the researchers, the region is of significant geopolitical importance, with several nations involved in territorial disputes and strategic competition.
The long-running nature of the campaign, dating back several years, suggests the operators are interested in sustained access to gather intelligence over extended periods. This pattern aligns with known state-sponsored cyber espionage tactics aimed at understanding military capabilities, strategies, and communications.
Attribution and State Sponsorship
Palo Alto Networks Unit 42 attributes the activity with high confidence to a threat group operating from China. The technical indicators, infrastructure patterns, and the strategic nature of the targets all point to a state-backed operation. The designation “STA” in the tracking code explicitly frames the motivation as government-sponsored.
China has consistently denied involvement in offensive cyber operations against other nations. Official statements from the Chinese government maintain that the country is a victim of cyber attacks and opposes all forms of cybercrime and cyber espionage.
Defensive Recommendations and Industry Response
Security researchers recommend that organizations, particularly in government and defense sectors, implement robust security measures. These include advanced endpoint detection and response (EDR) solutions capable of identifying memory-based attacks, strict application whitelisting, and comprehensive network monitoring for anomalous data transfers.
The disclosure of this campaign follows a pattern of increased visibility into state-aligned cyber activity in the Asia-Pacific region. Cybersecurity firms and government agencies worldwide continue to share threat intelligence to improve collective defense against such advanced persistent threats (APTs).
Looking ahead, cybersecurity analysts expect the threat group to continue refining its tools and techniques to maintain access to high-value targets. Further disclosures of technical indicators of compromise (IOCs) are anticipated, enabling a broader range of network defenders to hunt for related activity. International diplomatic discussions on establishing norms for state behavior in cyberspace are likely to reference these continued incidents of espionage.
Source: Palo Alto Networks Unit 42