A China-Linked advanced persistent threat (APT) group has been conducting a cyber espionage campaign against critical telecommunications infrastructure in South America since at least 2024. The threat actor is deploying a suite of three distinct malware implants to compromise Windows and Linux systems, as well as edge devices, according to research from Cisco Talos.
The security firm is tracking the activity under the identifier UAT-9244. Analysts assess this cluster is closely associated with another known APT group, FamousSparrow. This connection suggests a coordinated and sophisticated operation with significant resources.
Malware Arsenal and Attack Methods
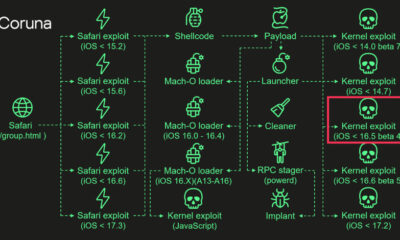
The attackers employ a trio of custom backdoors to maintain access to compromised networks. The primary implant, dubbed “TernDoor,” is designed for initial infection and remote control. A second tool, “PeerTime,” acts as a persistence mechanism and network reconnaissance utility.
A third component, “BruteEntry,” is used for credential theft and brute-force attacks to facilitate lateral movement within a victim’s environment. The use of multiple, specialized implants indicates a high level of planning and a focus on remaining undetected for long-term intelligence gathering.
Strategic Targets and Implications
The deliberate targeting of telecommunications providers represents a significant security concern. These companies form the backbone of national and international communications, hosting sensitive data and enabling connectivity for governments, businesses, and citizens.
Compromising such infrastructure can provide threat actors with the ability to intercept communications, gather intelligence on high-value targets, and potentially disrupt services. The focus on South America highlights the region’s growing geopolitical and economic importance, making it a focal point for state-sponsored cyber activity.
Cisco Talos has not publicly attributed the campaign to a specific Chinese entity but notes the strong technical links to previously observed China-nexus operations. The tactics, techniques, and procedures (TTPs) align with those of groups known to conduct cyber espionage for strategic national interests.
Industry and Government Response
Security researchers are disseminating indicators of compromise (IOCs) and detailed technical analysis to help network defenders identify and mitigate the threat. Telecommunications companies, particularly those in the affected region, are advised to review their security posture, monitor for the specified malware signatures, and enforce strict access controls.
National cybersecurity agencies in several countries are likely monitoring the situation. Such campaigns often prompt behind-the-scenes diplomatic discussions and increased information sharing between allied nations’ cyber defense units.
Looking ahead, cybersecurity experts expect the threat actor to continue refining its tools and tactics. The disclosure of this campaign may lead to a temporary shift in operations or the deployment of updated malware variants to evade detection. Ongoing vigilance and international cooperation will be essential to defend critical infrastructure against these persistent, state-aligned threats.
Source: Cisco Talos