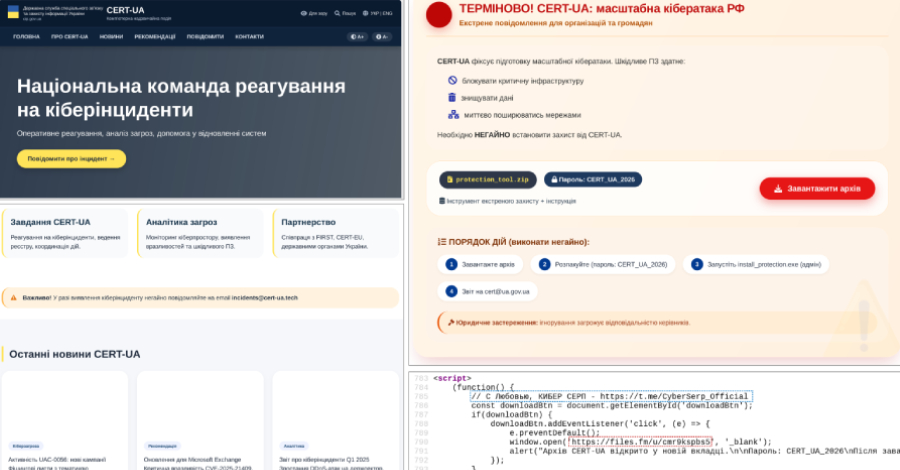
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed a widespread phishing campaign in which threat actors impersonated the cybersecurity agency to distribute malicious software. The attacks, which occurred on March 26 and 27, 2026, involved emails sent to approximately one million addresses, posing a significant risk to organizations and individuals by leveraging the trusted reputation of a national cyber defense body.
Details of the Attack Campaign
According to the official disclosure from CERT-UA, the threat actor group tracked as UAC-0255 was responsible for the operation. The attackers crafted emails designed to appear as legitimate communications from the Ukrainian CERT. These messages contained a password-protected ZIP archive that, when opened, deployed a remote administration tool identified as AGEWHEEZE.
This type of malware provides attackers with extensive control over a compromised system. It can enable data theft, surveillance, and further network infiltration. The use of a password-protected archive is a common evasion technique to bypass automated email security scanners that cannot inspect encrypted contents.
Implications of Agency Impersonation
The impersonation of a national computer emergency response team represents a serious escalation in social engineering tactics. CERT-UA is a authoritative source of security information and alerts within Ukraine. By mimicking this entity, the attackers significantly increased the likelihood that recipients would trust and interact with the malicious email.
This campaign undermines the vital trust relationship between cybersecurity agencies and the public they serve. It complicates future legitimate warnings, as users may become skeptical of authentic communications. The incident highlights a growing trend where attackers exploit the credibility of established institutions to enhance their phishing success rates.
Technical Analysis and Recommended Response
The AGEWHEEZE malware distributed in this campaign is classified as a Remote Access Trojan (RAT). Such tools are often used for persistent cyber espionage and data exfiltration activities. CERT-UA has published technical indicators of compromise, including file hashes and network signatures, to help organizations detect if their systems have been affected.
Security experts recommend that organizations treat any unsolicited email containing archives or executable files with extreme caution, even if they appear to come from a trusted source. Verification through secondary channels is advised. Individuals and IT departments should ensure security software is updated and conduct user awareness training focused on identifying sophisticated phishing attempts.
CERT-UA has not publicly attributed the UAC-0255 group to a specific nation-state or criminal organization. The broad targeting of one million email addresses suggests a large-scale intelligence gathering or cybercrime operation rather than a focused attack on a specific target.
Ongoing Investigation and Future Outlook
CERT-UA is actively investigating the campaign in coordination with international cybersecurity partners. The agency is expected to release further technical details and defensive recommendations as the analysis progresses. Law enforcement agencies in multiple jurisdictions may also be involved in tracking the perpetrators.
Moving forward, similar impersonation attacks targeting other national CERTs and trusted cybersecurity entities are considered highly probable. Organizations worldwide are urged to review their email security protocols and incident response plans. The cybersecurity community anticipates that threat actors will continue to refine these techniques, making ongoing vigilance and information sharing essential for defense.
Source: CERT-UA