-


Security
/ 4 weeks agoGoogle Confirms Active Exploitation of Android Graphics Flaw
Google disclosed on Monday that a high-severity security vulnerability affecting a Qualcomm component used in Android devices has been actively exploited....
-

Security
/ 4 weeks agoMicrosoft Warns of OAuth Phishing Targeting Government Entities
Microsoft issued a public warning on Monday regarding sophisticated phishing campaigns that are successfully bypassing standard email and browser security measures....
-


Security
/ 4 weeks agoNew Phishing Suite Bypasses MFA Using Reverse Proxy
cybersecurity researchers have identified a new and sophisticated phishing platform that is being used to circumvent multi-factor authentication protections. The toolkit,...
-


Security
/ 4 weeks agoAI Agents Emerge as Unmanaged Enterprise Force
A new class of powerful, autonomous artificial intelligence systems is rapidly being deployed within corporate environments, often operating outside of traditional...
-

Security
/ 4 weeks agoOpen-Source AI Tool Used in Global Fortinet Firewall Attacks
Security researchers have identified the use of an open-source, artificial intelligence-powered platform in a widespread campaign targeting network security appliances across...
-

Security
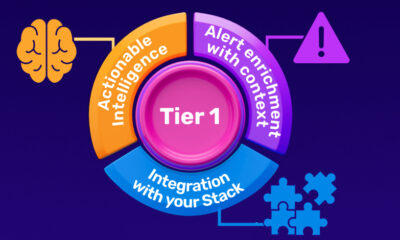
/ 4 weeks agoCISOs Face Critical Challenge in Building Effective Security Teams
Chief Information Security Officers globally are confronting a fundamental structural challenge within their Security Operations Centers, according to industry analysis. The...
-


Security
/ 4 weeks agoGoogle Develops Quantum-Resistant HTTPS for Chrome
Google has initiated a new program within its Chrome browser to protect the security of HTTPS certificates from future threats posed...
-


Security
/ 4 weeks agoChrome Vulnerability Allowed Malicious Extensions File Access
cybersecurity researchers have disclosed a critical security vulnerability in Google’s Chrome browser that has since been patched. The flaw, identified in...
-


Security
/ 4 weeks agoNorth Korean Hackers Deploy Malicious npm Packages in Global Campaign
cybersecurity researchers have identified a new phase of a persistent cyber espionage campaign, attributed to North Korean state-sponsored actors, involving the...
-


Security
/ 4 weeks agoAPT28 Exploited MSHTML Zero-Day Before Microsoft Patch
A critical vulnerability in Microsoft’s software was actively exploited by a state-sponsored hacking group before the company could release a security...


















