A sophisticated cyber espionage campaign, linked to a China-nexus threat actor, has been discovered targeting telecommunications networks to spy on government systems. The long-term operation involves the deployment of stealthy backdoor implants known as BPFDoor to maintain persistent access within critical infrastructure.
The activity has been attributed to a threat cluster tracked as Red Menshen, which is also known by the name Earth Bluecrow. Security researchers report that the group has strategically positioned itself within telecom environments, using these implants as a launchpad for further intrusions into sensitive government networks.
Stealth and Persistence in Critical Networks
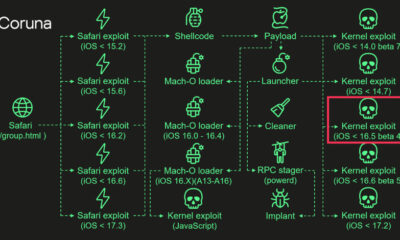
The campaign is characterized by its focus on establishing and maintaining hidden access points. The BPFDoor malware is a particularly stealthy tool, designed to evade common detection methods. It operates by leveraging the Berkeley Packet Filter (BPF) technology, a core component of the Linux kernel used for network traffic analysis.
By using this legitimate system feature for malicious purposes, the implants can hide their network communications, making them difficult for security software to identify. This allows the attackers to remain undetected for extended periods, sometimes years, while they conduct intelligence gathering operations.
Attribution and Known Tactics
Red Menshen, the group behind this campaign, is assessed by cybersecurity firms to have ties to China. The group is known for conducting cyber espionage that aligns with strategic intelligence priorities. Their focus on telecommunications providers is not new; such networks are high-value targets because they provide access to vast amounts of data and can serve as a gateway to other critical sectors.
The use of BPFDoor is a signature technique for this actor. The malware is deployed after initial network compromise, often following the exploitation of known vulnerabilities in public-facing servers or through spear-phishing attacks against network administrators.
Implications for Global Security
The infiltration of telecommunications infrastructure represents a significant national security concern for the affected countries. Telecom networks are considered part of a nation’s critical infrastructure, and compromise can enable surveillance of communications, data interception, and further attacks against government and private sector entities.
This campaign highlights a continuing trend where state-sponsored threat actors target the supply chain and service providers to reach their ultimate objectives. The strategic placement within a telecom network means any organization or individual using that provider’s services could be at potential risk.
Response and Mitigation
Cybersecurity agencies in multiple countries have likely been notified of these threats. Standard mitigation advice for such advanced persistent threats includes rigorous network segmentation, strict access controls, and continuous monitoring for anomalous network traffic patterns that might indicate the presence of a covert backdoor.
Security teams are advised to look for signs of BPFDoor implants, which include specific process names, network socket configurations, and the use of BPF filters that do not correspond to legitimate administrative activity. Patching known vulnerabilities in internet-facing systems remains a critical first line of defense.
Looking ahead, cybersecurity analysts expect continued monitoring and reporting on Red Menshen’s activities. International cooperation between government cyber defense units and private security firms is anticipated to deepen in response to this campaign. Further technical indicators of compromise and detailed analysis of the BPFDoor malware variants are likely to be published to aid network defenders worldwide.
Source: Multiple cybersecurity research reports