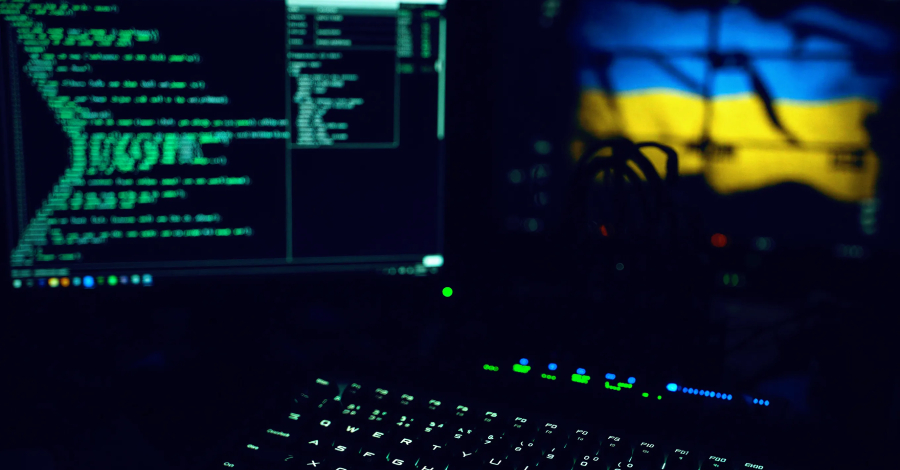
Cybersecurity researchers have identified a new Cyber Espionage campaign targeting Ukrainian organizations with previously undocumented malware. The operation, attributed to the Russian state-linked group APT28, employs two new malicious tools named BadPaw and MeowMeow to infiltrate systems.
The campaign was first detected in recent weeks, according to a technical analysis published by security researchers. The attacks are focused on entities within Ukraine, continuing a long-standing pattern of digital intrusions against the country amid the ongoing conflict.
Attack Methodology and Malware Details
The attack chain begins with a targeted phishing email. This email contains a link that directs the recipient to a downloadable ZIP archive. Once the archive is extracted and opened, an initial HTA (HTML Application) file executes.
This HTA file displays a decoy document written in Ukrainian. The lure document’s content relates to appeals concerning border crossing procedures, a topic designed to appear legitimate and urgent to a Ukrainian audience. This social engineering tactic aims to trick the target into enabling the malicious code.
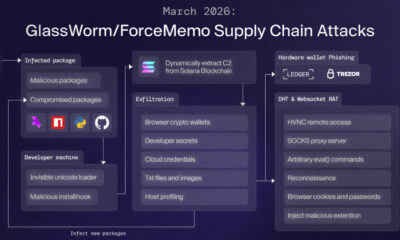
Upon execution, the HTA file deploys the first stage of the malware, identified as the BadPaw loader. The primary function of this loader is to establish a foothold on the compromised system and facilitate the deployment of additional, more sophisticated payloads.
The final payload delivered in this campaign is a backdoor named MeowMeow. A backdoor provides remote attackers with persistent, covert access to a victim’s computer. The MeowMeow backdoor allows the threat actors to steal data, execute commands, and maintain long-term surveillance of the infected network.
Attribution and Historical Context
Researchers attribute this activity to the advanced persistent threat group known as APT28. This group, also tracked under names like Fancy Bear and Sofacy, is widely believed by Western intelligence agencies and cybersecurity firms to operate under the direction of Russian military intelligence (GRU).
APT28 has a extensive history of conducting cyber espionage campaigns against governments, militaries, and critical infrastructure in Ukraine, NATO countries, and beyond. Their operations often align with Russian geopolitical interests, and they have been implicated in high-profile incidents including election interference campaigns and disruptive attacks.
The use of new, custom malware families like BadPaw and MeowMeow is a common tactic for such groups. It allows them to evade detection by traditional antivirus software that relies on known malware signatures, increasing the likelihood of a successful intrusion.
Implications and Recommended Response
The discovery of this campaign underscores the persistent and evolving cyber threat facing Ukrainian institutions. The use of relevant lure themes demonstrates careful reconnaissance and a focus on social engineering as an effective initial attack vector.
Security experts recommend that organizations, particularly those in sectors likely to be targeted, enhance their defensive measures. Key recommendations include employee training to identify sophisticated phishing attempts, the application of strict email filtering, and the use of endpoint detection and response (EDR) tools capable of identifying suspicious behavior rather than just known malware files.
Network segmentation and robust patch management are also critical to limit the potential damage from any successful breach. Organizations are advised to assume that sophisticated adversaries may already be present in their networks and to actively hunt for threats.
Based on the established patterns of APT28, cybersecurity analysts expect the group to continue refining its tools and tactics. Further technical details about the BadPaw loader and MeowMeow backdoor’s command and control infrastructure are likely to be published by the security community in the coming weeks as the investigation continues. Ukrainian cyber defense authorities are expected to issue updated advisories and indicators of compromise to help critical infrastructure defenders detect and block this specific threat.
Source: Cybersecurity Research Reports