A Russian state-linked hacking group has compromised thousands of small office and home office routers worldwide, repurposing them for a large-scale cyber espionage campaign. The group, tracked as APT28, also known as Forest Blizzard, has been exploiting insecure devices since at least May 2025 to conduct DNS hijacking attacks.
Security researchers have linked the campaign, codenamed “Endgame,” to the Russian General Staff Main Intelligence Directorate (GRU). The operation targets routers from brands like MikroTik and TP-Link that are left with default or weak administrative credentials.
Mechanics of the Router Hijacking
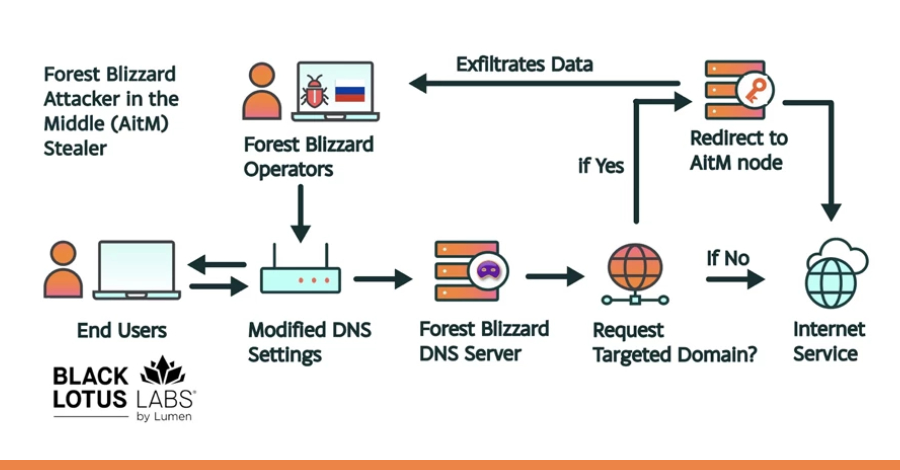
The threat actors scan the internet for vulnerable routers. Upon finding one, they use known default passwords or brute-force attacks to gain administrative access. Once inside, they alter the device’s Domain Name System (DNS) settings.
DNS acts as the internet’s phonebook, translating human-readable domain names into numerical IP addresses. By changing these settings, APT28 redirects users attempting to visit legitimate websites to malicious servers controlled by the hackers. This allows for credential theft and further network infiltration.
Scope and Impact of the Campaign
The campaign is global in scope, with compromised devices detected in North America, Europe, and Asia. The hijacked routers are used as a covert infrastructure layer, masking the origin of subsequent attacks on government, military, and corporate networks.
This technique provides the actors with significant operational advantages. It is low-cost, leverages widely available hardware, and makes attribution more difficult by routing traffic through everyday consumer devices in unrelated locations.
Historical Context and Attribution
APT28 is a well-established cyber espionage unit believed to operate on behalf of Russian military intelligence. The group has a long history of conducting sophisticated campaigns, including attacks against political organizations, government entities, and critical infrastructure sectors.
Security agencies in multiple countries have previously publicly attributed major cyber incidents to this actor. The use of compromised routers aligns with their known tactics of utilizing proxy networks to obscure their activities.
Mitigation and Security Recommendations
Network security experts urge all users and administrators of SOHO routers to take immediate action. The primary recommendation is to change the device’s default administrator password to a strong, unique passphrase. Firmware should also be updated to the latest version provided by the manufacturer.
Additionally, users should disable remote management features if they are not strictly necessary and consider using reputable DNS services, such as those offered by Cloudflare or Google, directly on the router. Organizations are advised to monitor their network traffic for unexpected DNS requests.
Ongoing Investigation and Next Steps
International cybersecurity firms and government Computer Emergency Response Teams (CERTs) are actively tracking the campaign. They are working to identify all compromised devices and notify internet service providers, who can then alert their customers.
Law enforcement agencies are expected to continue their investigations into the command and control infrastructure used by APT28. Security analysts predict the group will continue to evolve its tactics, potentially targeting other classes of internet-connected devices as awareness of this specific router campaign grows.
Source: Multiple cybersecurity research reports and government advisories.