Security researchers have identified a previously undocumented banking trojan targeting financial institutions. The malware, named TCLBANKER, is capable of attacking 59 banking, fintech, and cryptocurrency platforms. Elastic Security Labs is tracking this activity under the codename REF3076.
The TCLBANKER trojan is assessed to be a major update of the Maverick malware family. This earlier variant is known to use a worm called SORVEPOTEL to spread through messaging and email systems. The new variant represents a significant evolution in capability and scope.
Infection Vectors and Spread Mechanisms
The trojan spreads through malicious links and attachments distributed via WhatsApp and Microsoft Outlook. Attackers are using social engineering techniques to convince victims to click on these links. Once a device is infected, the malware gains access to sensitive financial data.
TCLBANKER is designed to intercept credentials and two factor authentication codes. It can also manipulate web sessions to redirect funds. The malware targets a wide array of platforms, including major banking apps and cryptocurrency exchanges based in Brazil and internationally.
Technical Capabilities
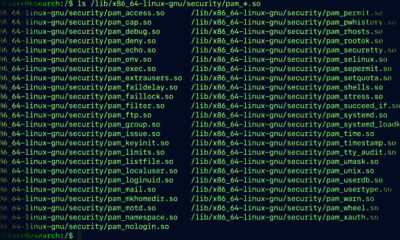
Analysis shows that TCLBANKER employs advanced code obfuscation to evade detection. It uses overlay attacks to mimic legitimate banking interfaces. When a user opens a targeted banking app, the trojan displays a fake login screen to capture credentials.
The malware also has the ability to read SMS messages and push notifications. This allows it to intercept one time passwords and transaction confirmations. It can also block incoming calls to prevent banks from contacting victims directly.
Attribution and History
Researchers link TCLBANKER to the same threat actors behind the Maverick malware family. The SORVEPOTEL worm component is a key differentiator. This worm automatically forwards itself to the victim’s contacts, enabling rapid spread through trusted communication channels.
The Brazilian origin of the malware is notable. Brazil has been a frequent target for banking trojans due to its large and active digital banking sector. The adaptation to target cryptocurrency platforms indicates a shift toward broader financial exploitation.
Implications for Users
The use of WhatsApp and Outlook as delivery vectors makes the trojan particularly dangerous. These platforms are used daily by millions of people worldwide. Users who receive unexpected messages with links or attachments should verify the sender’s identity before interacting.
Security experts recommend enabling multi factor authentication that does not rely solely on SMS. Hardware security keys or authenticator apps provide stronger protection against session hijacking. Users should also keep their devices and security software up to date.
Financial institutions are being advised to monitor for anomalous login patterns. They should implement behavioral analysis to detect overlay attacks. The banking sector is likely to see increased collaboration with cybersecurity firms to counter this emerging threat.
Further analysis of TCLBANKER is ongoing. Elastic Security Labs is expected to release additional technical details as the investigation progresses. The malware’s modular architecture suggests that future variants may add new capabilities and target additional platforms.
Source: Elastic Security Labs