Security researchers have disclosed details of a new local privilege escalation vulnerability in the Linux kernel, designated as an unpatched flaw that allows attackers to gain root access on major distributions. The issue, referred to as Dirty Frag, is being described as a successor to a recently disclosed and actively exploited vulnerability known as Copy Fail.
The underlying flaw, tracked as CVE-2026-31431, carries a CVSS score of 7.8, indicating a high severity level. The original vulnerability, Copy Fail, was already under active exploitation in the wild before the emergence of this new variant.
Vulnerability Details and Impact
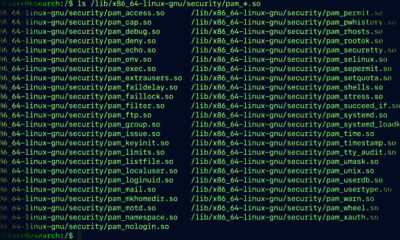
Dirty Frag exploits a weakness in the Linux kernel’s handling of fragmented network packets, which can lead to memory corruption. An attacker with local access to a vulnerable system can trigger this condition to elevate their privileges to root, bypassing standard user account restrictions.
The flaw affects a broad range of Linux distributions, including enterprise and consumer versions. Researchers have confirmed that systems running unpatched kernels are susceptible, and no official fix has been released by kernel maintainers at the time of disclosure.
Comparison to Copy Fail
Copy Fail, the predecessor vulnerability, was initially reported to Linux kernel maintainers and later saw active exploitation in live environments. Dirty Frag leverages a related but distinct vector, making it a direct follow up to that earlier security issue. Security analysts note that the emergence of an improved version of a recently exploited flaw underscores the ongoing challenge of securing the kernel’s complex networking stack.
Affected Systems and Potential Risks
Major Linux distributions such as Ubuntu, Debian, Fedora, and CentOS are likely affected, along with many other distributions that use the mainline kernel. The vulnerability requires an attacker to have local access to the target machine, which reduces the immediate risk for remote attack scenarios. However, once an attacker gains a foothold on a system through other means, Dirty Frag can be used to achieve full system compromise.
Organizations running Linux servers or workstations are advised to monitor kernel updates closely. The exploit does not require authentication beyond standard user credentials, making it a powerful tool for attackers already inside a network perimeter.
Response from Maintainers
The vulnerability was reported to Linux kernel maintainers by the researchers who discovered it. At the time of this report, no official patch or workaround has been provided. The development community is expected to work on a fix, but a timeline for a stable kernel update has not been announced.
Users are advised to limit local access to systems and apply any future kernel patches as soon as they become available. Until a patch is released, system administrators may consider implementing additional access controls and monitoring for suspicious local activity that could indicate an exploitation attempt.
Outlook and Next Steps
Given that Copy Fail is already under active exploitation, security experts anticipate that Dirty Frag could similarly become a target for cybercriminals and penetration testers. The lack of a current patch places the burden on system administrators to use mitigation strategies such as restricting user permissions and enabling security modules like SELinux or AppArmor.
The Linux kernel community is expected to prioritize a fix in upcoming releases, but no official timeline has been provided. Until a patch is issued, affected distributions will need to weigh the risk of exposure against the operational demands of running unmodified kernels.
Source: Delimiter Online