A new analysis of over 25 million security alerts from operational enterprise environments has revealed a systemic problem within security operations centers. Defenders are routinely ignoring a significant portion of these warnings, particularly those classified as informational or low-severity. The findings, drawn from live data across 10 million monitored endpoints, indicate that a “one missed threat per week” pattern is more than anecdotal; it is a verified industry norm.
The dataset behind this report highlights a troubling gap in enterprise defense strategies. While high-severity alerts often trigger immediate investigation, the sheer volume of lower-tier warnings creates an environment where analysts are forced to prioritize. This results in a high number of false negatives regarding low-severity threats, which can serve as a foothold for more dangerous attacks.
The report suggests that security teams have quietly institutionalized a practice of not looking at these alerts. This is not a failure of individual analysts, but rather a structural outcome of alert fatigue. With millions of events generated daily, many of which are benign, the human element becomes the bottleneck. The data supports the conclusion that a missed low-severity threat occurs every week on average across these monitored environments.
Understanding the Alert Volume
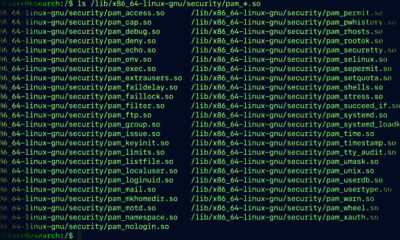
The investigation analyzed alerts from a broad spectrum of live enterprise networks. The 10 million monitored assets generated a massive stream of data, with the majority of alerts falling into the informational or low-severity categories. This volume makes manual review impractical, leading to the use of automated filtering and escalation rules that often fail to catch subtle indicators of compromise.
Security experts note that low-severity alerts are often dismissed because they lack obvious malicious indicators. However, these alerts frequently represent reconnaissance activity, misconfigurations, or early stages of an attack chain. Ignoring them allows attackers to establish persistence or gather intelligence without triggering high-alert systems.
Implications for Security Operations
The findings challenge the assumption that current security stacks are effective against sophisticated threats. The report indicates that many organizations are operating with a false sense of security, believing that their systems catch everything important. In reality, a significant gap exists between the volume of data generated and the capacity to analyze it effectively.
This pattern of missed alerts has direct consequences. Attackers increasingly target low-severity signals to evade detection. By bypassing high-severity triggers, they can operate within the noise of everyday operations. The data suggests that without a fundamental change in how alerts are triaged, this vulnerability will persist.
Reevaluating Detection Strategies
The report calls for a shift in detection strategies. Rather than focusing solely on high-severity incidents, organizations need to improve the contextual analysis of low-severity alerts. This could involve better correlation tools, behavioral analytics, or machine learning models that can identify patterns across vast datasets.
Experts argue that the human analyst cannot be replaced entirely, but the process must be augmented to handle the scale. Reducing the noise requires better alert tuning and prioritization algorithms that assess risk dynamically, rather than relying solely on static severity labels.
The findings underscore a need for transparency in how security vendors define alert severity. If informational alerts are routinely ignored, the value of those signals is effectively zero. The report suggests that enterprises must demand more actionable data from their security tools.
Looking ahead, the industry is expected to move toward automated response systems that can handle low-severity threats without human intervention. However, this requires a high degree of confidence in the system’s ability to distinguish between a true positive and noise. The timeline for such advancements remains uncertain, but the data from this report provides a clear benchmark for the current state of security operations.
Source: Delimiter