Cybersecurity researchers have identified a new botnet derived from the Mirai malware, self-identified as xlabs_v1, which is actively targeting internet-connected devices that have the Android Debug Bridge (ADB) feature enabled. The goal of the operation is to recruit these devices into a network used for launching distributed denial-of-service (DDoS) attacks.
The discovery was made by threat analysts at Hunt.io, who detailed the findings in a recent report. The investigation began after the researchers identified an exposed directory on a server hosted in the Netherlands. This directory contained the malware’s source code and configuration files, revealing the botnet’s infrastructure and operational methods.
ADB is a legitimate command-line tool included in the Android software development kit. It allows developers to communicate with an Android device for debugging and testing purposes. However, when ADB is left enabled and exposed to the public internet on port 5555, it becomes a significant security vulnerability. Attackers can connect to the device without authentication, gaining full remote control.
How the Botnet Operates
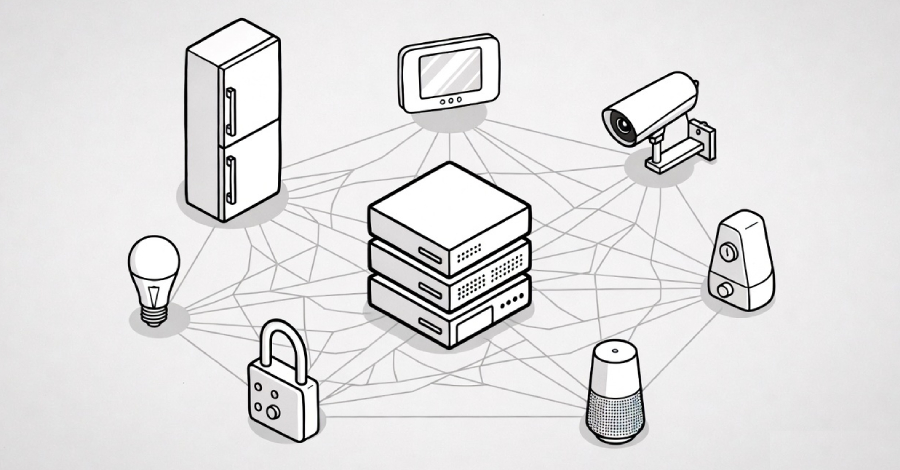
The xlabs_v1 botnet is a variant of the infamous Mirai malware, which first emerged in 2016 and has since been used as a blueprint for numerous other botnets. Mirai works by scanning the internet for vulnerable devices, typically Internet of Things (IoT) hardware, and then using default or weak credentials to gain access. Once infected, the device becomes part of a botnet that can be commanded to flood a target with traffic, causing a DDoS outage.
In the case of xlabs_v1, the initial infection vector is not weak passwords but the exposed ADB service. The botnet scanner identifies devices with port 5555 open and attempts to connect directly. Upon successful connection, it deploys the malware payload, which then establishes persistent control and connects to a command-and-control (C2) server.
Researchers noted that the malware leverages a self-identifying string, xlabs_v1, in its binary, which distinguishes it from other Mirai derivatives. The botnet appears to be in an active development phase, with the exposed directory providing insight into ongoing modifications.
Infrastructure and Targeting
Hunt.io identified the C2 server for the botnet is also hosted in the Netherlands. The exposed directory on this server contained not only the malware binaries but also lists of previously scanned and compromised devices. This data helps researchers understand the botnet’s growth and its geographic targeting strategy.
The primary targets appear to be a wide range of consumer IoT devices that run on Android or Android-derived operating systems. This includes smart TVs, set-top boxes, Android-based thin clients, and even some older smartphones that are connected to the internet. Many of these devices are left unpatched and often have ADB enabled by default for development purposes, making them low-hanging fruit for attackers.
The DDoS capabilities of the botnet are significant. Based on the source code analysis, xlabs_v1 can execute several attack vectors, including HTTP floods, UDP floods, and TCP SYN floods. These attacks can overwhelm a target server or network, rendering it inaccessible to legitimate users.
For owners of IoT devices, the primary risk remains the exposure of ADB to the internet. Security best practices dictate that ADB should only be enabled during active development and should never be exposed on a public network. If a device is not intended for development, the service should be permanently disabled.
The discovery highlights a growing trend in IoT security. As consumer devices become more complex, the number of potential attack vectors increases. The Mirai malware family has proven to be highly adaptable, with new variants like xlabs_v1 emerging to exploit novel vulnerabilities.
Looking ahead, researchers expect the operators of xlabs_v1 to refine the malware further. The exposure of the C2 directory may prompt the attackers to change infrastructure or encryption methods to avoid future detection. The botnet represents a persistent threat to the IoT ecosystem, and device manufacturers are urged to ensure that features like ADB are disabled by default in production firmware.
Source: Hunt.io