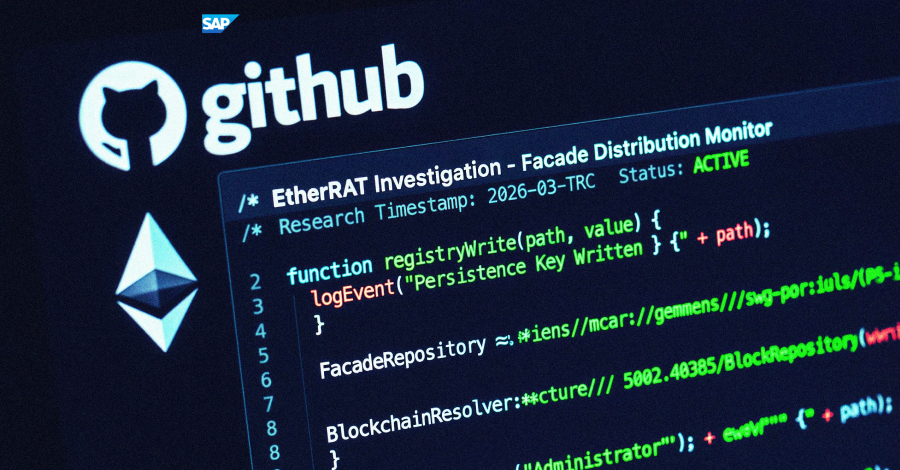
A sophisticated cyberattack campaign that spoofs legitimate administrative tools to target enterprise professionals has been uncovered by researchers. The operation, identified by the Atos Threat Research Center (TRC) in March 2026, specifically aims at high-privilege accounts belonging to system administrators, DevOps engineers, and security analysts.
The attackers are using deceptive facades on the GitHub platform. These facades impersonate well known utilities that these professionals rely on for daily operations. By creating convincing replicas of administrative tools and publishing them on GitHub, the threat actors aim to trick victims into downloading malware.
Attack Vector and Methodology
The campaign, tracked as EtherRAT, integrates advanced Search Engine Optimization (SEO) techniques to increase its visibility. The malicious repositories are designed to appear high in search results, making them more likely to be discovered by professionals seeking specific software solutions.
Once a victim downloads the spoofed tool, the EtherRAT malware is deployed. This remote access trojan gives attackers control over the infected system. It allows them to steal credentials, move laterally across networks, and exfiltrate sensitive data. The focus on high-privilege users suggests the attackers are seeking access to critical infrastructure and confidential information.
Targeted Professionals and Tools
The attack is not random. It is carefully calibrated to exploit the trust that administrators and engineers place in common development and system management utilities. By masquerading as these specific tools, the malware bypasses typical security checks that might flag unknown executables.
Researchers at Atos TRC noted the high level of sophistication in the campaign. The GitHub facades are not simple copies; they include proper documentation, repository stars, and even fake issue trackers to build legitimacy. This level of detail suggests a well-funded and organized threat group.
Implications for enterprise security
For organizations, this campaign underscores the growing risk of supply chain attacks targeting the software development ecosystem. Enterprise security teams must verify the authenticity of tools downloaded from public repositories. This can involve checking repository ownership, verifying digital signatures, and using hashes to confirm file integrity against official sources.
The targeting of administrative and security roles is a significant concern. Compromising a single administrator account can allow attackers to bypass multiple layers of security. Companies should implement strict security protocols for privileged users, including multi-factor authentication and least privilege access controls.
Recommendations for Protection
Security experts recommend that organizations monitor for suspicious activity related to tool downloads. IT departments should maintain a whitelist of approved software sources. Any downloads from public platforms like GitHub should be scrutinized thoroughly, especially those that appear through search engine results rather than direct links from official vendor websites.
Employee training is also a critical defense. Professionals should be educated about the specific risks of downloading tools from unverified sources. They should be trained to verify the official repository or website of a tool before downloading it, paying close attention to the account that published the repository.
The EtherRAT campaign is a reminder that cybercriminals are constantly adapting their methods to target the most trusted sources in the technology ecosystem. The combination of SEO poisoning and platform abuse on GitHub creates a significant challenge for defenders.
Looking ahead, it is likely that similar campaigns will continue to emerge, using increasingly sophisticated social engineering techniques. Platforms like GitHub may need to implement stronger verification measures for tool publishers. Enterprise security teams should prepare for this threat by strengthening their software supply chain security and improving detection capabilities for rogue repositories.
Source: Atos Threat Research Center