cybersecurity researchers have disclosed a critical security vulnerability affecting GitHub.com and GitHub Enterprise Server. The flaw, designated as CVE-2026-3854, enables an authenticated user to achieve remote code execution by issuing a single “git push” command.
The vulnerability carries a CVSS score of 8.7, marking it as a high severity issue. It has been classified as a command injection vulnerability, a type of attack where an adversary can execute arbitrary commands on a host operating system.
Technical Details of CVE-2026-3854
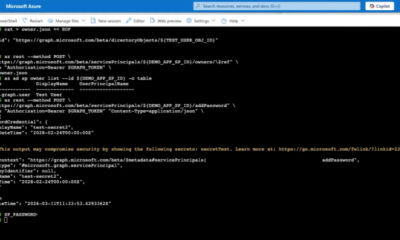
The core of the vulnerability lies in how GitHub processes certain inputs during the push operation. An attacker who holds push access to a repository can exploit this flaw to inject and execute commands on the underlying server infrastructure.
Command injection vulnerabilities are particularly dangerous because they can allow an attacker to move from a limited user context to full system control. In this case, the attack vector is streamlined. The attacker does not need social engineering or multiple steps. A single push action is sufficient to trigger the exploit.
The flaw impacts both the cloud hosted GitHub.com platform and the self hosted GitHub Enterprise Server. This means organizations running their own instances are equally exposed if they do not apply the available patch.
Who is Affected and What Actions Are Required
All GitHub users and organizations that host repositories are potentially affected if the attacker can gain push access to a repository. Push access can be obtained through compromised credentials, insider threats, or misconfigured repository permissions.
GitHub has released a security advisory and a patch for the vulnerability. Users and administrators of GitHub Enterprise Server are advised to update to the latest patched version immediately. GitHub.com users do not need to take action, as the platform is updated centrally.
Organizations should also review their repository access controls. Limiting push access to trusted collaborators and enabling two factor authentication can reduce the risk of exploitation.
Broader Implications for the Software Supply Chain
This vulnerability highlights ongoing risks in modern software development workflows. The git push command is a fundamental operation for developers. A flaw in this core function could allow an attacker to compromise not just a repository, but potentially the entire build and deployment pipeline.
In a supply chain attack scenario, an attacker could inject malicious code into a project that is then distributed to end users. The severity of this flaw is magnified by the widespread reliance on GitHub as a central hub for open source and private code repositories.
Security teams should treat this vulnerability with high priority. While the exploit requires authenticated push access, the low complexity of the attack makes it attractive to threat actors.
Timeline and Next Steps
GitHub has not disclosed whether this vulnerability has been exploited in the wild prior to disclosure. Researchers are expected to publish a detailed technical analysis in the coming weeks, which may lead to proof of concept exploit code becoming public.
Organizations running GitHub Enterprise Server should schedule an immediate patching window. Those relying on GitHub.com should verify that their security teams are monitoring for any anomalous push activity.
Industry observers expect that the cybersecurity community will closely analyze this vulnerability for similar patterns in other version control systems and CI/CD tools.
Source: Delimiter