A security flaw in a built-in administrative role within Microsoft Entra ID could have Allowed attackers to escalate privileges and take over service principals, researchers have warned.
The vulnerability was discovered by Silverfort, a cybersecurity firm, and relates to the “Agent ID Administrator” role. This role was introduced by Microsoft as part of its agent identity platform, designed to manage the identity lifecycle of artificial intelligence agents.
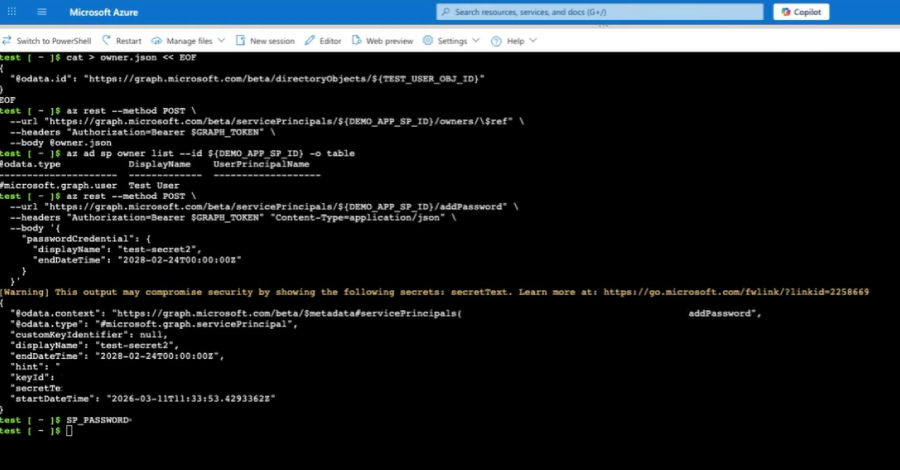
According to the findings, the Agent ID Administrator role grants excessive permissions that could be exploited. An attacker who gains control of an account with this role could modify the credentials and authentication methods of any service principal in the tenant.
This flaw creates a direct path to Privilege Escalation. A compromised Agent ID Administrator account could be used to take over highly privileged service principals, including those with Global Administrator rights. This effectively allows an attacker to control the entire identity infrastructure.
Microsoft has addressed the vulnerability. The company has updated the permissions associated with the Agent ID Administrator role to remove the ability to update credentials and authentication methods for service principals. This change prevents the specific escalation path identified by Silverfort.
The role itself is relatively new and not widely assigned. However, as organizations increasingly deploy AI agents, the use of this role may grow. The discovery highlights the risks associated with new, powerful roles that may not have been fully vetted for security implications.
Silverfort’s research demonstrates how a role intended for AI agent management could be repurposed for malicious activity. The firm emphasized the importance of reviewing role permissions and applying the principle of least privilege, ensuring that administrators have only the access they need to perform their specific tasks.
Background on the Agent ID Administrator Role
The Agent ID Administrator role is part of Microsoft’s push to support AI agent workloads within Entra ID. Agents, whether for customer service or internal automation, require digital identities to access resources. This role was designed to centralize the management of these identities.
The role included permissions to update credentials, such as passwords and certificates, for any service principal. Silverfort found that this permission was not scoped to agent principals but applied globally. This meant a user with the role could modify any service principal in the directory, including those with elevated privileges.
Implications for Organizations
For organizations using Entra ID, this finding underscores the need for continuous auditing of administrative roles. Security teams should review who is assigned the Agent ID Administrator role and consider if its full permission set is necessary.
Microsoft’s patch effectively neuters the specific attack vector. However, the incident serves as a cautionary tale about the potential dangers of granting broad permissions to roles designed for emerging technologies. Administrators are advised to monitor Microsoft’s documentation for further changes to this or similar roles.
Next Steps and Recommendations
Microsoft has not disclosed any evidence of this flaw being exploited in the wild. The update has been applied to all tenants. Organizations do not need to take action to receive the security update, but they should verify that their internal security policies are updated to reflect the reduced permission scope of the role.
Security experts recommend that companies using Entra ID conduct a review of all privileged role assignments. They should also consider implementing conditional access policies and monitoring for unusual credential changes to service principals, as these could be indicators of an attempted attack using previously assigned permissions.
Source: Silverfort