A new industry report has identified a specific technical bottleneck that may be stalling many enterprise Zero Trust security implementations: the secure movement of data between systems. The findings, published by cybersecurity research firm Cyber360, challenge a long standing assumption that simply connecting a system solves the underlying security problem.
The report, titled “Defending the Digital Battlespace,” is based on a survey of 500 security professionals across multiple sectors. It reveals that most security programs operate on the premise that once a system is connected to a network, the security challenge is addressed. However, researchers argue that this assumption is fundamentally flawed and is a major reason why Zero Trust adoption often fails to progress.
Flawed Assumptions About Connectivity
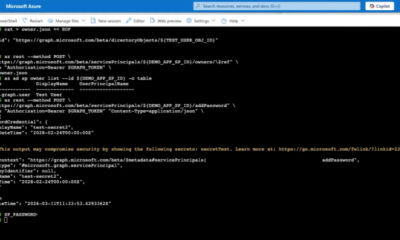
The core issue, according to the survey data, lies in the transition from connection to data transfer. Many organizations focus heavily on securing endpoints and verifying user identities but neglect the security of the data as it moves between services. This oversight creates a significant vulnerability that attackers can exploit.
The research indicates that the process of opening a ticket, standing up a gateway, and pushing data through is not sufficient for a Zero Trust architecture. This approach relies on a perimeter based security model, which is the opposite of the “never trust, always verify” principle that defines Zero Trust.
Survey respondents reported that the technical and procedural overhead required to securely move data between different security zones, or even between cloud environments, is a primary cause of program delays. The complexity of maintaining consistent security policies for data in transit across disparate systems is proving to be a major operational hurdle.
Impact on Security Programs
The report suggests that organizations which fail to address this data movement bottleneck will continue to see their Zero Trust initiatives stall. This delay leaves networks vulnerable to lateral movement attacks, where a compromised system is used to access other parts of the network.
Security teams are increasingly realizing that Zero Trust is not just about access control, but about continuous verification of data integrity and security throughout its lifecycle. The failure to secure the “last mile” of data transit effectively undermines the entire security framework.
The study emphasizes that without a robust strategy for secure data movement, the security perimeter remains porous. This finding is particularly relevant for organizations that rely on microservices architectures, APIs, and cloud based data pipelines.
Recommendations from the Research
While the report does not endorse specific products, it outlines several key areas that organizations should address. These include implementing data level encryption that persists across all transitions, not just at the network layer. It also recommends the use of strict data tagging and classification to enforce policies based on content, not just context.
Furthermore, the report calls for a shift in mindset from “connect and trust” to “verify and protect” at every stage of data exchange. This involves investing in tools that can inspect, log, and control data as it moves, rather than simply trusting the channel it travels on.
The Cyber360 report serves as a warning that the industry has underestimated the complexity of data movement security. As digital transformation accelerates, this bottleneck is expected to become more pronounced.
Expected Next Steps
Industry observers expect that the findings will push security vendors to develop more integrated solutions focused on data in transit. Future standards and protocols are likely to place a greater emphasis on data level security controls that are independent of network architecture.
Organizations are advised to conduct a full audit of their data transfer workflows. The goal is to identify where security policies are applied and where gaps exist. The next twelve months are likely to see a surge in demand for technologies that can provide end to end security for data movement without compromising performance.
Source: Cyber360