Security researchers have issued a warning that the cybercriminal group behind VECT 2.0 ransomware is unintentionally operating as a data wiper due to a critical flaw in its encryption system. The flaw, present across Windows, Linux, and ESXi variants, permanently destroys files larger than 131 kilobytes, making recovery impossible even for the attackers themselves.
Technical Implementation Failure Creates Permanent Data Loss
The issue stems from how VECT 2.0 handles file encryption. According to threat hunters who analyzed the malware, the ransomware attempts to encrypt data in chunks. However, for files exceeding the 131KB threshold, the encryption routine fails to complete properly. Instead of locking the file for ransom, the process corrupts the data irreversibly.
This means the VECT 2.0 locker is functionally more similar to a wiper than traditional ransomware. Victims facing an infection cannot regain access to large files by paying a ransom, as the threat actors possess no key or method to restore the destroyed data.
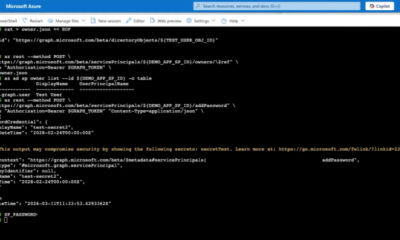
Affected Platforms and Attack Vectors
The vulnerability affects all known variants of the malware targeting Windows, Linux, and VMware ESXi environments. Researchers have observed that the flaw is consistent across these platforms, suggesting it is a fundamental error in the software’s code rather than a platform specific bug.
Initial reports indicate that VECT 2.0 typically gains initial access through unsecured remote desktop protocols and phishing campaigns. Once inside a network, the ransomware spreads laterally, targeting file servers, databases, and virtual machines. The destructive nature of the encryption tool means that any large backup files or critical databases within the 131KB limit are at high risk of permanent loss.
Implications for Ransomware Negotiation and Recovery
This discovery has significant implications for incident response teams and cybersecurity professionals. The standard advice in ransomware incidents is to preserve encrypted files in case a decryption key becomes available through law enforcement or security research. However, with VECT 2.0, this strategy is futile for large files.
Organizations hit by VECT 2.0 must now treat affected systems as total losses for any data exceeding the size limit. Forensic analysis of the malware confirms that the data is not recoverable through any known method, including paying the ransom. The threat actors themselves cannot reverse the damage caused by their own tool.
Recommendations for Defense and Mitigation
Cybersecurity firms are urging organizations to prioritize offline backups that are not continuously connected to the network. For systems running Linux and ESXi environments, strict access controls and network segmentation are recommended to limit the lateral movement capabilities of the ransomware.
Additionally, security teams should monitor for indicators of compromise associated with VECT 2.0, including unusual encryption processes and file renaming patterns. Early detection remains the most effective defense against this destructive variant. The fact that the ransomware effectively wipes data rather than encrypting it highlights the importance of having immutable backup solutions that are air gapped from the primary network.
Ongoing Analysis and Future Outlook
Security researchers continue to analyze the VECT 2.0 codebase to determine if the flaw can be exploited for broader detection signatures. The discovery has prompted a reassessment of ransomware response playbooks, as the wiper like behavior shifts the incident from a data extortion scenario to a disaster recovery operation.
Organizations are advised to update their incident response plans to account for the permanent data destruction caused by this variant. Law enforcement agencies have been notified, and further technical advisories are expected from private cybersecurity firms as more details emerge about the threat group’s infrastructure and methods.
Source: Delimiter