cybersecurity researchers have uncovered a large scale telecommunications fraud operation that uses fake CAPTCHA verification prompts to trick users into sending premium rate international text messages, generating illicit revenue for the threat actors behind the scheme.
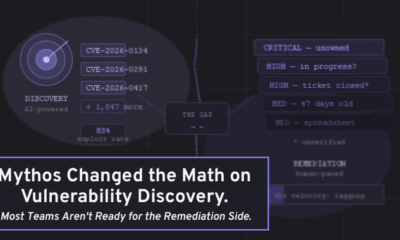
The operation, detailed in a new report from Infoblox, involves over 120 malicious advertising campaigns run using the Keitaro traffic distribution system. These campaigns are designed to deceive victims across the globe into unknowingly subscribing to costly SMS services.
The scam begins when a user visits a compromised or malicious website. Instead of a standard CAPTCHA challenge to prove they are human, the site presents the user with a request to confirm their phone number. This interface closely mimics the appearance of a legitimate CAPTCHA test, complete with distorted text and interactive elements. However, the underlying code is malicious.
How the CAPTCHA Deception Works
When a user interacts with the fake CAPTCHA, typically by clicking a verification button or entering displayed characters, the site automatically sends a premium rate SMS from the user’s mobile device. The scam relies on the fact that mobile browsers can initiate SMS messages via specific HTML or JavaScript commands, often without requiring the user’s explicit confirmation.
The fraud is particularly effective because the visual trick is deceptive. Many users associate CAPTCHA tests with security, not charges. The malicious code is hidden behind a familiar interface, catching victims off guard.
The scheme operates on a subscription model. The SMS initiated by the fake CAPTCHA enrolls the victim in a recurring service that charges their mobile bill. Victims may not notice the charges until their next billing statement. The threat actors lease phone numbers in various countries to receive the revenue from these premium rate calls and messages.
Keitaro Campaigns at the Core
Infoblox researchers identified at least 120 distinct Keitaro campaigns driving traffic to these fake CAPTCHA pages. Keitaro is a legitimate traffic distribution and tracking platform often used for advertising. However, in this case, threat actors are using it as a cloaking system to direct users from legitimate ad networks or search results to the fraudulent pages.
These campaigns are global in scope, affecting users in North America, Europe, and parts of Asia. The geographic targeting suggests the attackers are focusing on regions where premium rate SMS services are common and where mobile billing systems allow such charges to be applied with minimal oversight.
Financial Impact and Revenue Model
The financial structure of the scam is noteworthy. The threat actors do not directly profit from the fake CAPTCHA interaction. Instead, they lease phone numbers from telecommunications providers at wholesale rates. They then charge the victim’s mobile account at a much higher premium rate. The difference between the wholesale cost of the SMS route and the premium charged to the victim is the illicit profit.
Each individual charge is relatively small, often a few dollars. However, the scale of the campaign is significant. With over 120 campaigns running simultaneously, the cumulative profit from millions of victims can be substantial. Because the charges appear as standard mobile bills, many victims do not immediately contest them, allowing the attackers to collect revenue for months.
Global Nature of the Fraud
The operation is not contained to one country. The use of leased phone numbers from multiple providers enables the attackers to target victims in different regions simultaneously. The Keitaro platform allows them to rotate landing pages based on the victim’s location, language, or device type, increasing the effectiveness of the attack.
The scam represents a sophisticated evolution of SMS fraud. In the past, similar attacks relied on malware or direct phishing links. This method uses a social engineering trick that abuses user trust in a common security protocol.
Users should be cautious about any website that requests their phone number in a CAPTCHA test. Legitimate CAPTCHA services from Google or other providers do not require a phone number for standard verification. If a site asks for a phone number or appears to be sending an SMS without clear user action, it is likely fraudulent.
Telecommunications providers and mobile carriers are aware of the issue. However, the sheer number of campaigns and the ability of attackers to quickly change domains and routes makes disruption difficult.
Moving forward, researchers expect the threat actors to expand their operations. The use of Keitaro as a distribution platform suggests a high degree of organization. Similar attacks using different social engineering pretexts, such as fake two factor authentication prompts or account verification notices, may emerge. Infoblox recommends that users enable billing restrictions on mobile accounts and review monthly statements for unexpected charges to mitigate the risk of falling victim to this scam.
Source: Infoblox