Google released an emergency security update for its Chrome web browser on Thursday to address a critical vulnerability that is already being exploited by attackers. The update, part of a broader patch set fixing 21 security flaws, is intended to protect users worldwide from potential compromise.
The actively exploited flaw is tracked as CVE-2026-5281. Google has classified it as a high-severity issue. The vulnerability is a use-after-free bug located within Dawn, an open-source component that provides a cross-platform implementation of the WebGPU standard for hardware-accelerated graphics and computation.
Technical Details of the Vulnerability
A use-after-free vulnerability occurs when a program continues to use a memory pointer after it has been freed or deallocated. This can corrupt valid data or allow an attacker to execute arbitrary code on a target system. In this instance, the flaw exists in the Dawn component, which handles WebGPU operations within Chrome.
WebGPU is a modern web standard designed to provide high-performance 3D graphics and data-parallel computation. Its implementation is complex and interacts closely with a computer’s graphics hardware, making it a potentially attractive target for security researchers and malicious actors.
Scope and Impact of the Exploitation
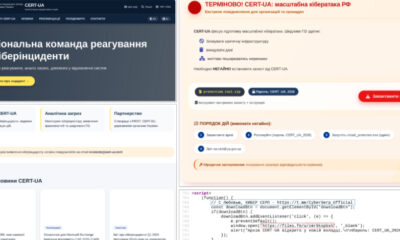
Google’s threat analysis group confirmed that exploits for CVE-2026-5281 exist “in the wild,” meaning attackers are actively using them against real users. The company has not disclosed technical details of the attacks, the identity of the threat actors, or the scale of the exploitation. This is standard practice to prevent further abuse while the patch is being distributed.
The vulnerability affects Chrome versions prior to the update released on Thursday. Users on Windows, macOS, and Linux platforms are all potentially at risk if they are running an outdated version of the browser.
Google’s Response and User Action
In response to the active threats, Google has pushed out version 130.0.6723.116 for Windows and macOS, and version 130.0.6723.116 for Linux. The updates will roll out automatically over the coming days and weeks. However, users can manually check for and install the update immediately to ensure protection.
To update Chrome manually, users should click the three-dot menu in the top-right corner, navigate to “Help,” and then select “About Google Chrome.” The browser will then check for and apply any available updates, requiring a restart to complete the process.
This marks the first zero-day vulnerability patched in Chrome in 2026. Google maintains a consistent policy of rapidly developing and releasing fixes for such critical flaws once they are discovered, either by internal security teams or through external reporting.
Broader Security Context
The Thursday update addressed a total of 21 security issues. While CVE-2026-5281 was the only flaw confirmed to be under active attack, the other patched vulnerabilities include a range of high and medium-severity bugs. These include other use-after-free errors in components like the V8 JavaScript engine and the ANGLE graphics layer, as well as heap buffer overflows and inappropriate implementations.
Google frequently rewards external security researchers who report vulnerabilities through its Chrome Vulnerability Reward Program. The company acknowledged the contributions of multiple external researchers in identifying the other flaws fixed in this update.
Looking ahead, users and enterprise administrators should expect the patched version of Chrome to become the stable release across all platforms within a short timeframe. Security experts typically recommend applying software updates, especially for web browsers, as soon as they are available to mitigate the risk of exploitation. Google is likely to continue monitoring for any further exploitation attempts and may release additional information if the threat landscape changes significantly.
Source: Google Chrome Releases