cybersecurity researchers have identified a novel and sophisticated payment card skimmer that leverages WebRTC data channels to evade standard security defenses on e-commerce websites. The discovery was detailed in a report published this week by the security firm Sansec. This technique marks a significant evolution in the methods used by cybercriminals to steal sensitive financial information from online shoppers.
Bypassing Content Security Policies
The malware, described as a WebRTC skimmer, operates by exploiting a common security feature known as a Content Security Policy, or CSP. Many websites implement CSPs to restrict the sources from which scripts can be loaded, effectively blocking unauthorized code. According to the report, this new skimmer circumvents these restrictions by using WebRTC, a technology typically employed for real-time communication like video chats, to establish a direct data channel.
“Instead of the usual HTTP requests or image beacons, this malware uses WebRTC data channels to load its payload and exfiltrate stolen payment data,” Sansec stated. This method allows the malicious code to communicate with a command and control server without triggering alerts from traditional CSP rules designed to monitor web requests.
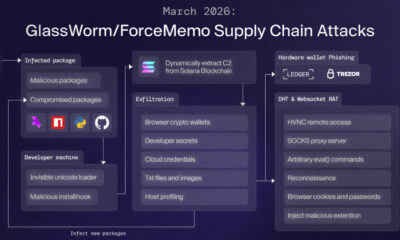
Technical Execution of the Attack
The attack begins when a compromised e-commerce site unknowingly serves the skimming code to a customer’s browser during the checkout process. Once executed, the code initiates a WebRTC connection. This peer-to-peer channel is then used to fetch the final stage of the skimming payload directly from an attacker-controlled server, a process that standard CSPs often do not govern.
After the full skimmer is loaded, it monitors input fields on the payment page. When a customer enters their credit card number, expiration date, and CVV code, the skimmer captures this data. The stolen information is subsequently transmitted back to the attackers through the same WebRTC data channel, completing the exfiltration.
Increasing Sophistication of Magecart Attacks
This development is part of a broader trend within the realm of Magecart attacks, where threat actors inject skimming scripts into online stores. Security experts note that attackers are continuously innovating to bypass improved security measures deployed by website operators and security vendors. The use of WebRTC represents a move towards abusing legitimate, built-in web technologies that are essential for modern web functionality, making detection more challenging.
Implications for Online Security
The emergence of this technique has immediate implications for the security of online transactions. It demonstrates that even robust security policies like CSPs can have blind spots. For e-commerce businesses, this underscores the necessity of a defense-in-depth strategy that includes multiple layers of security monitoring beyond basic CSP implementation.
For consumers, the threat remains largely invisible. The checkout process appears normal, with no obvious signs of compromise. This reinforces the importance of using secure payment gateways and services that offer additional fraud protection, such as tokenization or one-time use card numbers.
Industry and Researcher Response
Following the disclosure, security teams are analyzing the method to develop new detection signatures and mitigation strategies. The report from Sansec provides technical indicators of compromise that other security firms and internal IT teams can use to scan their web properties for similar threats. The broader cybersecurity community is now examining WebRTC permissions and their potential for abuse in other attack scenarios.
Looking Ahead: Mitigation and Next Steps
In response to this new threat vector, security professionals recommend that website administrators review and potentially tighten their CSP directives to account for WebRTC connections where applicable. Continuous monitoring of website code for unauthorized changes, especially on payment pages, remains a critical defense. Furthermore, security vendors are expected to update their web application firewalls and intrusion detection systems to recognize malicious WebRTC signaling patterns. As attackers refine this technique, ongoing collaboration between researchers, platform providers, and e-commerce operators will be essential to develop effective countermeasures and protect global payment ecosystems.
Source: Sansec