cybersecurity researchers have identified a significant evolution in the GlassWorm supply-chain attack, which now abuses the Open VSX registry to compromise software developers. The campaign, active as of recent reports, represents a major shift in tactics by exploiting trusted extension dependencies to propagate malware. This development matters because it directly threatens the security of integrated development environments (IDEs) and the integrity of open-source software projects globally.
Exploiting Extension Trust
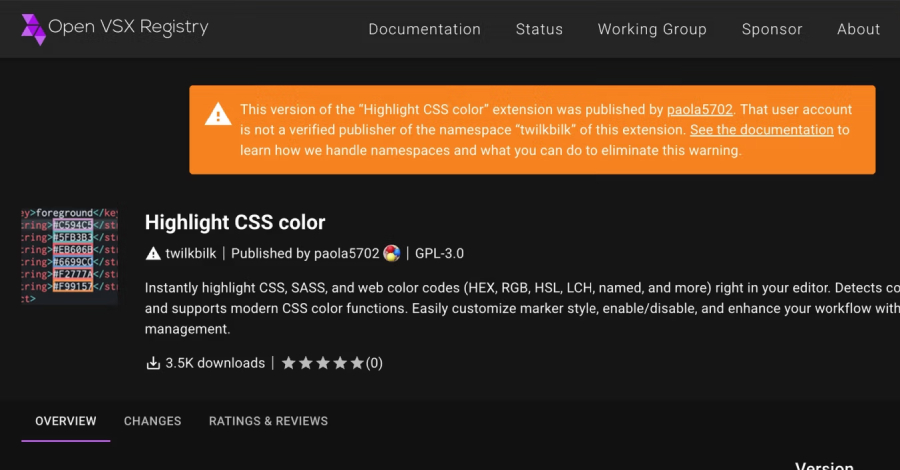
According to security analysts, the threat actors behind GlassWorm have moved away from a method where each malicious extension contained the full payload. Their new strategy leverages the “extensionPack” and “extensionDependencies” features within the Open VSX ecosystem. These features are designed to allow developers to bundle useful tools together or declare required components.
In this updated attack, the hackers publish what appears to be a legitimate, standalone extension. This initial extension, however, contains a dependency on another, malicious package. When a developer installs the seemingly harmless extension, the system automatically downloads and installs the dependent malicious package from the registry. This technique, known as a transitive dependency attack, effectively turns benign extensions into Trojan horses.
Scale and Impact of the Campaign
The campaign has been linked to the compromise of at least 72 different extensions on the Open VSX registry. Open VSX is an open-source alternative to Microsoft’s Visual Studio Marketplace, commonly used with IDEs like VSCodium and Eclipse Theia. By targeting this registry, the attackers aim to infiltrate the development workflows of a wide range of programmers.
The ultimate payload of these malicious extensions is a loader for a known backdoor called SeroXen. This remote access trojan (RAT) provides attackers with full control over an infected system. They can then steal sensitive data, credentials, and source code, or deploy additional malware. The attack chain is particularly insidious because it abuses the inherent trust developers place in community-driven code repositories.
Industry and Platform Response
The Eclipse Foundation, which oversees the Open VSX registry, has been notified of the malicious activity. The organization’s security team is actively working to identify and remove the compromised extensions. They have also initiated reviews of their submission and vetting processes to prevent similar abuses in the future.
Security firms that uncovered the campaign have advised developers to exercise extreme caution. Recommendations include scrutinizing extension dependencies before installation, verifying publisher reputations, and maintaining updated security software. The incident has sparked broader discussions about the security challenges inherent in software supply chains, especially within open-source ecosystems that rely on communal trust.
Looking Ahead: Mitigation and Next Steps
Security researchers expect the attackers to continue refining their methods, potentially targeting other developer platforms and package managers. The immediate next steps involve a comprehensive purge of the identified malicious extensions from the Open VSX registry and the dissemination of indicators of compromise (IOCs) to the wider security community. Developers who may have installed affected extensions are urged to scan their systems and rotate any exposed credentials. The long-term response will likely involve platform operators implementing more robust security checks for dependency declarations to restore trust in these essential developer resources.
Source: Adapted from cybersecurity research reports