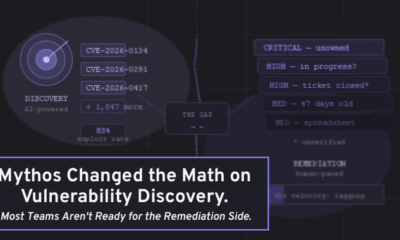
A fundamental shift is underway in how organizations should prioritize identity security work, moving away from traditional IT ticket methods toward a mathematical risk-based model. This change is driven by the increasing complexity of modern digital environments, which are no longer dominated by human users in controlled settings.
The Limitations of Traditional Prioritization
For years, many identity and access management programs have prioritized tasks using methods common in IT support: focusing on the volume of requests, the loudness of stakeholder complaints, or simply addressing items that have failed a compliance control check. Industry analysis indicates this reactive approach is becoming ineffective.
The breakdown occurs as enterprise environments evolve. When systems were primarily accessed by a static, fully onboarded workforce within a corporate network, simple prioritization could suffice. Modern infrastructure, however, includes complex mixes of human and machine identities, third-party contractors, cloud services, and internet-facing applications.
Components of Modern Identity Risk
Security professionals now define identity risk as a compound calculation built from multiple independent factors. These factors must be evaluated together to understand the true threat level.
The first factor is control posture, which refers to the technical and policy safeguards already in place, such as multi-factor authentication or privileged access management. The second is hygiene, encompassing the ongoing maintenance of identity systems, like the timely deprovisioning of accounts for departed employees.
Business context forms the third critical component. This involves understanding the sensitivity of the data or systems an identity can access. A standard user account in a marketing system presents a different risk profile than an administrator account for financial databases.
The final, and most challenging, factor to assess is intent. This relates to determining whether an identity’s actions are legitimate or malicious, a process increasingly aided by behavioral analytics and machine learning tools.
Implications for Security Teams
The move toward a risk-math model requires security teams to develop new competencies. It necessitates the collection and correlation of data from disparate sources, including human resources systems, cloud platforms, network logs, and application directories.
This integrated view allows for the scoring of identity risks based on the confluence of factors. For example, an account with weak password hygiene accessing a business-critical system from an unusual location would generate a high-risk score, prompting immediate investigation.
This approach stands in contrast to simply working through a long backlog of generic “identity tasks.” It aims to direct limited security resources toward the situations that pose the greatest potential for financial loss, data breach, or operational disruption.
Future Developments and Industry Direction
The identity security sector is responding to this conceptual shift. Major conferences and industry publications are increasingly featuring discussions on quantitative risk models for access management. Several established security vendors and new market entrants are developing products designed to automate the collection and analysis of risk signals.
Industry observers expect this trend to accelerate as regulatory frameworks continue to emphasize the principle of least privilege and robust access controls. The next phase of development will likely focus on standardizing risk calculations and improving the integration of threat intelligence to better assess the intent factor.
Organizational adoption is projected to grow, though the pace may vary by industry. Sectors with stringent compliance requirements or those holding highly sensitive data, such as finance and healthcare, are anticipated to be early adopters of these advanced identity risk prioritization methodologies.
Source: Industry Analysis